Companies utilize IPsec Virtual Private Network (VPN) to interconnect between two locations across an IP Wide Area Network (WAN) or across the Internet. If you haven’t tried using this service you can download VPN here. Load balancing allows companies to fully access available bandwidth between IPsec VPN sites over Equal Cost Multi-Path (ECMP) or Link Aggregation Group (LAG).
Below is a short guide on how to load balance IPsec protocol over VPN tunnels to improve load-balancing of IPsec ESP traffic.
Setting The Load Balancing Method
Set the following load balancing command to balance or distribute data during a session:
config load-balance setting
set dp-load-distribution-method {to-master | src-ip | dst-ip | src-dst-ip | src-ip-sport | dst-ip-dport | src-dst-ip-sport-dport}
endFlow Rules
You may not be able to balance some types of data. Therefore, if you cannot load balance a certain type of data, then send it to the primary FPM. You can do this by configuring flow rules for the traffic.
Create your flow rules by utilizing the config load balance flow-rule command. The default configuration utilizes this command to send IKE, GRE, session helper, Kerberos, BGP, RIP, IPv4, and IPv6 DHCP, PPTP, BFD, IPv4 multicast and IPv6 multicast to the primary FPM.
The following configuration sends all IKE sessions to the primary FPM:
config load-balance flow-rule
edit 1
set status enable
set vlan 0
set ether-type ip
set protocol udp
set src-l4port 500-500
set dst-l4port 500-500
set action forward
set forward-slot master
set priority 5
set comment "ike"
next
edit 2
set status disable
set vlan 0
set ether-type ip
set protocol udp
set src-l4port 4500-4500
set dst-l4port 0-0
set action forward
set forward-slot master
set priority 5
set comment "ike-natt src"
next
edit 3
set status disable
set vlan 0
set ether-type ip
set protocol udp
set src-l4port 0-0
set dst-l4port 4500-4500
set action forward
set forward-slot master
set priority 5
set comment "ike-natt dst"How to Determine the Primary FPM
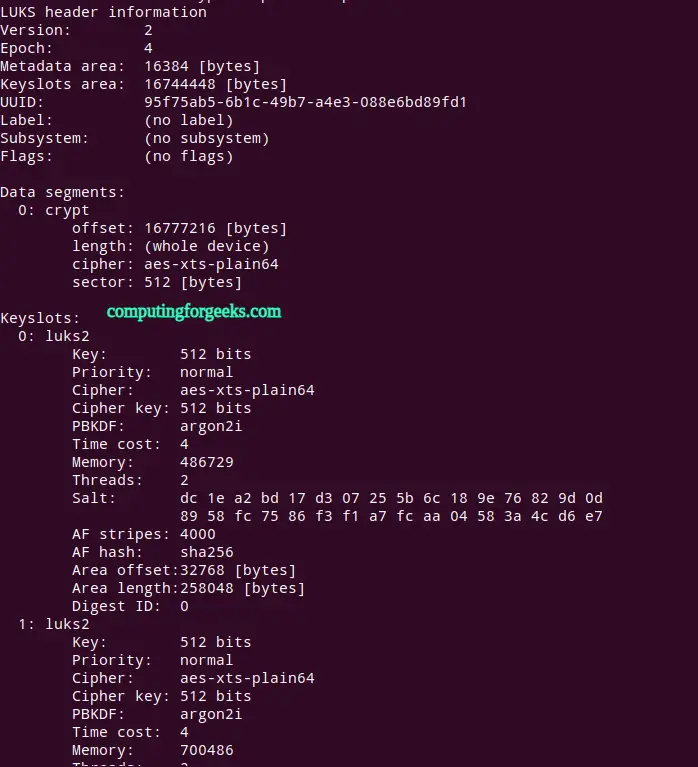
The primary FPM carries out dynamic routing. Therefore, you can use the diagnose load-balance status command to choose which FPM is designated as the principal FPM.
The example below demonstrates a diagnosis of the load-balance status output. It reveals that the FPM – in the case, in slot 3 – is the primary or master FPM of the module.
Slot: 2 Module
FIM02: FIM04E3E16000222
Master FPM Blade: slot-3
Slot 3: FPM20E3E17900133
Status:Working Function:Active
Link: Base: Up Fabric: Up
Heartbeat: Management: Good Data: Good
Status Message: "Running"
Slot 4:
Status:Dead Function:Active
Link: Base: Up Fabric: Down
Heartbeat: Management: Failed Data: Failed
Status Message: "Waiting for management heartbeat."IPsec VPN Load Balancing
You can use the following command to enable or disable IPsec VPN load balancing:
config load-balance setting
config ipsec-load-balance {disable | enable}
endBy default IPsec, VPN load balancing is enabled and the flow rules listed below are disabled. So the IPsec VPN sessions are directed to the DP2 processors and load balanced to the FPMs. However, IPsec VPN load balancing enabled, IPsec VPN sessions traveling between two IPsec tunnels will be dropped because the two IPsec tunnels may be terminated on different FPMs.
So, if you have traffic entering the device from one IPsec VPN tunnel and leaving the device out another IPsec VPN tunnel you need to disable IPsec load balancing:
config load-balance setting
config ipsec-load-balance disable
endThe following flow rules are enabled if IPsec VPN load balancing is disabled:
config load-balance flow-rule
edit 22
set ether-type ipv4
set protocol udp
set src-l4port 500-500
set dst-l4port 500-500
set comment "ipv4 ike"
next
edit 23
set ether-type ipv4
set protocol udp
set src-l4port 4500-4500
set comment "ipv4 ike-natt src"
next
edit 24
set ether-type ipv4
set protocol udp
set dst-l4port 4500-4500
set comment "ipv4 ike-natt dst"
next
edit 25
set ether-type ipv4
set protocol esp
set comment "ipv4 esp"
next
endThese flow rules should generally handle all IPsec VPN traffic for VPN tunneling protocols. You can also adjust them or add your own flow rules if you have an IPsec VPN setup that is not compatible with the default flow rules.
GTP load balancing
You can use the following command to enable or disable GTP load balancing.
config load-balance setting
config gtp-load-balance {disable | enable}
endBy default, this option is disabled and GTP load balancing is disabled. The following flow rule is enabled and GTP traffic is directed to the primary (master) FPM.
config load-balance flow-rule
edit 17
set ether-type ipv4
set protocol udp
set dst-l4port 2123-2123
set comment "gtp-c to master blade"
next
endWhen the gtp-load-balance option is enabled, the GTP load balancing is flow rule is disabled and GTP sessions are directed to the DP2processors and load balanced to the FPMs.
Default Configuration For Traffic That Cannot Be Load Balanced
The following flow rules are recommended to handle common forms of traffic that cannot be load balanced. These flow rules send GPRS (port 2123), SSL VPN, IPv4 and IPv6 IPsec VPN, ICMP and ICMPv6 traffic to the primary (or master) FPM.
The CLI syntax below just shows the configuration changes. All other options are set to their defaults. For example, the flow rule option that controls the FPM slot that sessions are sent to is forward-slot and in all cases below forward-slot is set to its default setting of master. This setting sends matching sessions to the primary (or master) FPM.
config load-balance flow-rule
edit 20
set status enable
set ether-type ipv4
set protocol udp
set dst-l4port 2123-2123
next
edit 21
set status enable
set ether-type ip
set protocol tcp
set dst-l4port 10443-10443
set comment "ssl vpn to the primary FPM"
next
edit 22
set status enable
set ether-type ipv4
set protocol udp
set src-l4port 500-500
set dst-l4port 500-500
set comment "ipv4 ike"
next
edit 23
set status enable
set ether-type ipv4
set protocol udp
set src-l4port 4500-4500
set comment "ipv4 ike-natt src"
next
edit 24
set status enable
set ether-type ipv4
set protocol udp
set dst-l4port 4500-4500
set comment "ipv4 ike-natt dst"
next
edit 25
set status enable
set ether-type ipv4
set protocol esp
set comment "ipv4 esp"
next
edit 26
set status enable
set ether-type ipv6
set protocol udp
set src-l4port 500-500
set dst-l4port 500-500
set comment "ipv6 ike"
next
edit 27
set status enable
set ether-type ipv6
set protocol udp
set src-l4port 4500-4500
set comment "ipv6 ike-natt src"
next
edit 28
set status enable
set ether-type ipv6
set protocol udp
set dst-l4port 4500-4500
set comment "ipv6 ike-natt dst"
next
edit 29
set status enable
set ether-type ipv6
set protocol esp
set comment "ipv6 esp"
next
edit 30
set ether-type ipv4
set protocol icmp
set comment "icmp"
next
edit 31
set status enable
set ether-type ipv6
set protocol icmpv6
set comment "icmpv6"
next
edit 32
set ether-type ipv6
set protocol 41
endMore articles in our site:



![Install Kali Linux 2026.1 Step by Step [Full Guide] 3 Install Kali Linux 2026.1 Step by Step [Full Guide]](https://computingforgeeks.com/wp-content/uploads/2026/03/install-kali-linux-20261-step-by-step-768x403.png)

I’m confused by what applications are involved in the above workflow?