This is a continuation article for setting up a personal VPN with Algo VPN. In our previous post, we coved the installation of Algo VPN server. This article will focus on how you can connect to the Algo VPN Server from Linux and Android devices.
If you are connected to an insecure Network and you have an Algo VPN server instance in the cloud, you can always connect securely through it via your Android or Linux device. This article takes you through the whole process of connecting you to the Algo VPN instance. Let us cruise through.
Connecting to Algo VPN using an Android Device
Follow the steps below to connect your Android device to Algo VPN instance running on premise or in the clloud.
Install WireGuard VPN client
Go over to play store and search for WireGuard App. When you find it, go ahead and install it. This tutorial will cover QR Code

Download QR Image from the Algo Server
The QR Images for the various users we had set-up when installing Algo server are located in a directory under the unzipped algo-master file. It will be found under:
/algo-master/configs//wireguard/USER.pngDownload the desired image to your local computer using either scp or sftp commands. Once it is downloaded, proceed to the next step.
Connection Set Up
Open the installed WireGuard App and click on the plus + button to set-up a new connection.

Tap on the Create from QR code option as shown below.

Scan the downloaded QR Image most likely on your the screen of your local computer image viewer at the moment.
You will get a
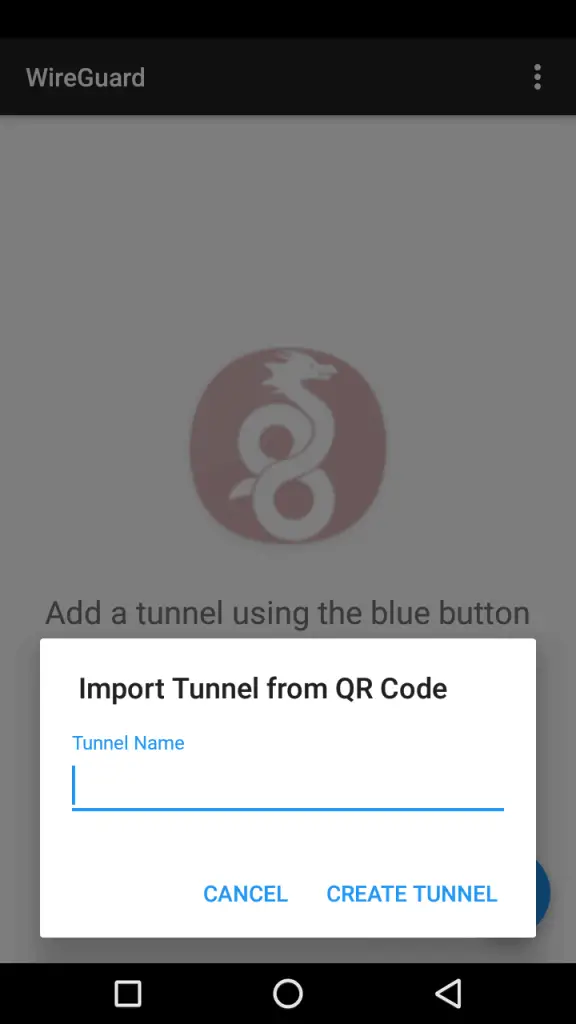
A connection request pop up will ensue. Just tap on ok and we are good to go. After the profile has been added, you can just swipe the profile’s tap box to the right wen you have your Wi-Fi connected to enjoy secure VPN from your Algo server in the cloud.
To prove that your traffic is going through your VPN server, just search for whatismyip.com and look at the public ip returned. It should be the one of your Algo VPN Server.
Connecting to Algo VPN using on Linux
For connecting to Algo VPN from a Linux machine, we will demo with Ubuntu system.
Step One: Add Wireguard’s repository
sudo add-apt-repository ppa:wireguard/wireguardStep Two: Install WireGuard
After the repository is successfully added and system updated, go ahead and install Wireguard in your Ubuntu box
sudo apt update
sudo apt install wireguardStep Three: Download/Copy Wireguard user config file from Algo Server
Log into your Algo server via sftp or any other utility such as scp and download one configuration file for a wireguard user you would like to use.
The config files are under /algo-master/configs/<PUBLIC IP>/wireguard/USER.conf. After you have it in your client Ubuntu box you can make a few adjustments to it if the following describes your client.
If the client is running Bionic (or another Linux that uses systemd-resolved for DNS) you should first edit the config file. Comment out the line that begins with DNS = and replace it with:
After you have it in your client Ubuntu box you can make a few adjustments to it if the following describes your client. If the client is running Bionic (or another Linux that uses systemd-resolved for DNS) you should first edit the config file. Comment out the line that begins with DNS = and replace it with:
PostUp = systemd-resolve -i %i --set-dns=172.16.0.1 --set-domain=~.I did not edit the config file in my set up. I left it the way it was.
Step Four: Configure WireGuard
Finally, install the config file on your client as /etc/wireguard/wg0.conf and start WireGuard:
sudo install -o root -g root -m 600 jack.conf /etc/wireguard/wg0.conf Replace jack.conf with your configuration file.
Step Five: Start the WireGuard VPN Session and check if it is running
Run the following commands to start the WireGuard VPN Session.
sudo systemctl start wg-quick@wg0
sudo systemctl status wg-quick@wg0 You should be able to see something like below if it is running
$ systemctl status wg-quick@wg0
● [email protected] - WireGuard via wg-quick(8) for wg0
Loaded: loaded (/lib/systemd/system/[email protected]; disabled; vendor preset: enabled)
Active: active (exited) since Sat 2024-02-09 23:46:31 EAT; 12s ago
Docs: man:wg-quick(8)
man:wg(8)
https://www.wireguard.com/
https://www.wireguard.com/quickstart/
https://git.zx2c4.com/WireGuard/about/src/tools/man/wg-quick.8
https://git.zx2c4.com/WireGuard/about/src/tools/man/wg.8
Process: 7048 ExecStart=/usr/bin/wg-quick up %i (code=exited, status=0/SUCCESS)
Main PID: 7048 (code=exited, status=0/SUCCESS) To confirm that the VPN Connection is up, do :
curl ipv4.icanhazip.com The above command will display the public IP of your Algo VPN server. Alternatively you can run the following command.
$ sudo wg
sudo: unable to resolve host cloud
interface: wg0
public key: Y7AHdeFWOI2Zlx0jmxniMFNmcjld0Qivi61eF/bQeXw=
private key: (hidden)
listening port: 53762
fwmark: 0xca6c
peer: yv77/3optaIp/poGrlCHHCbetXvI1OGLybbJggKLkXk=
endpoint: :51820
allowed ips: 0.0.0.0/0, ::/0
latest handshake: 1 minute, 14 seconds ago
transfer: 3.34 KiB received, 3.18 KiB sent
persistent keepalive: every 25 seconds Another way to confirm the connection was successful is to check your network interfaces. You will notice an interface like the one below:
wg0: mtu 1420 qdisc noqueue state UNKNOWN group default qlen 1
link/none
inet 10.19.49.4/24 scope global wg0
valid_lft forever preferred_lft foreverTo setup other Linux systems as clients, check Linux client setup documentation.
Other VPN related articles:
- How to Setup IPSec VPN server with L2TP and Cisco IPsec on Ubuntu / CentOS / Debian
- Easy Way to Install and Configure OpenVPN Server on Ubuntu
- How to use nmcli to connect to OpenVPN Server on Linux
- How to connect to VPN Server with OpenConnect SSL VPN Client on Linux