FreeIPA is a free and open source identity management platform sponsored by Red Hat. It is the upstream project for Red Hat Identity Manager (IdM). FreeIPA bundles 389 Directory Server, MIT Kerberos, Dogtag Certificate System, and BIND DNS into a single integrated solution for managing users, hosts, services, authentication, and access policies across Linux environments.
This guide walks through a full FreeIPA Server deployment on Rocky Linux 10, AlmaLinux 10, or RHEL 10. We cover DNS and hostname configuration, package installation, the interactive server setup, firewall rules, Web UI access, enrolling the first client, managing users and groups, and setting up HBAC and sudo policies.
Benefits of FreeIPA
- Central Authentication – Manage users, hosts, and services across large Linux/Unix environments from one place.
- Fine-grained Access Control – Define host-based access control (HBAC) policies and delegate administrative tasks precisely.
- Two-Factor Authentication (2FA) – Built-in support for One Time Passwords (OTP) alongside Kerberos tickets.
- Active Directory Trust – Establish cross-forest Kerberos trusts so AD users can access IPA-managed resources without separate accounts.
- Integrated PKI – Dogtag Certificate System provides CA services, certificate issuance, revocation lists, and OCSP out of the box.
- Integrated DNS – BIND with LDAP backend for automatic service record management and DNS zone provisioning.
FreeIPA Server Components
FreeIPA Server is built on these open source projects.
- 389 Directory Server – Multi-master LDAPv3 directory providing the central data store.
- MIT Kerberos KDC – Single sign-on authentication for users and services.
- Dogtag Certificate System – Internal CA and RA for certificate lifecycle management.
- ISC BIND – DNS server with LDAP backend for automatic SRV record management.
- Apache httpd – Hosts the FreeIPA Web UI and JSON-RPC API.
- SSSD – System Security Services Daemon for client-side caching and authentication.
- Chronyd – NTP client to keep time synchronized across the realm.
Prerequisites
- A server running Rocky Linux 10, AlmaLinux 10, or RHEL 10 with a fresh minimal installation
- At least 4 GB RAM (installations with less RAM frequently fail during CA setup)
- 2 or more vCPUs
- 10 GB free disk space minimum
- A fully qualified domain name (FQDN) resolvable via DNS or
/etc/hosts - Ports 80, 443, 88, 464, 389, 636, and 53 not in use by other applications
- Root or sudo access
Step 1: Set Hostname and DNS Resolution
FreeIPA requires a properly configured FQDN. The hostname must be a subdomain of the domain you intend to manage, for example ipa.example.com for the example.com domain. Set the hostname first.
sudo hostnamectl set-hostname ipa.example.comVerify the hostname is set correctly.
$ hostnamectl --static
ipa.example.comIf you do not have a DNS server resolving this hostname, add it to /etc/hosts. Replace 10.0.1.10 with the actual server IP address.
echo "10.0.1.10 ipa.example.com ipa" | sudo tee -a /etc/hostsConfirm the FQDN resolves to the correct IP.
$ ping -c 2 ipa.example.com
PING ipa.example.com (10.0.1.10) 56(84) bytes of data.
64 bytes from ipa.example.com (10.0.1.10): icmp_seq=1 ttl=64 time=0.031 ms
64 bytes from ipa.example.com (10.0.1.10): icmp_seq=2 ttl=64 time=0.058 ms
--- ipa.example.com ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1001ms
rtt min/avg/max/mdev = 0.031/0.044/0.058/0.013 msThe FQDN must not resolve to 127.0.0.1 or ::1. If it does, FreeIPA installation will fail. Make sure the /etc/hosts entry uses the real network IP before the hostname.
Step 2: Configure Timezone and System Updates
Kerberos authentication is time-sensitive. Ensure your timezone is correct before proceeding.
sudo timedatectl set-timezone Africa/NairobiReplace Africa/Nairobi with your timezone. List all available timezones with timedatectl list-timezones. Then update the system packages.
sudo dnf update -yReboot if a new kernel was installed.
sudo systemctl rebootStep 3: Install FreeIPA Server on Rocky Linux 10 / AlmaLinux 10 / RHEL 10
On RHEL 10 and its derivatives, FreeIPA server packages are available directly from the AppStream repository. No module streams are needed. The packages install as standard RPMs.
sudo dnf install -y freeipa-serverTo include integrated DNS (recommended for most deployments), also install the DNS component.
sudo dnf install -y freeipa-server-dnsFor Active Directory trust support, add the trust packages as well.
sudo dnf install -y freeipa-server-trust-adVerify the installed FreeIPA version.
$ ipa --version
VERSION: 4.12.2, API_VERSION: 2.262Step 4: Run the FreeIPA Server Installation
The ipa-server-install command runs an interactive setup that configures all FreeIPA components. If you installed the DNS packages, include the --setup-dns flag.
Option A: Install with Integrated DNS (Recommended)
sudo ipa-server-install --setup-dnsOption B: Install without DNS
If you already have a dedicated DNS server managing your zone, skip DNS integration.
sudo ipa-server-installThe installer will prompt you for several values. Here is the expected interaction when using --setup-dns.
The log file for this installation can be found in /var/log/ipaserver-install.log
This program will set up the IPA Server.
Version 4.12.2
This includes:
* Configure a stand-alone CA (dogtag) for certificate management
* Configure the NTP client (chronyd)
* Create and configure an instance of Directory Server
* Create and configure a Kerberos Key Distribution Center (KDC)
* Configure Apache (httpd)
* Configure DNS (named)
* Configure the KDC to enable PKINIT
To accept the default shown in brackets, press the Enter key.
Server host name [ipa.example.com]: <Press Enter to confirm>
Please confirm the domain name [example.com]: <Press Enter to confirm>
Please provide a realm name [EXAMPLE.COM]: <Press Enter to confirm>
Directory Manager password: <Enter a strong password>
Password (confirm): <Confirm password>
IPA admin password: <Enter a strong password>
Password (confirm): <Confirm password>
Do you want to configure DNS forwarders? [yes]: yes
Enter an IP address for a DNS forwarder: 8.8.8.8
Enter an IP address for a DNS forwarder: 1.1.1.1
Enter an IP address for a DNS forwarder (empty to skip):
Do you want to search for missing reverse zones? [yes]: <Press Enter>
Do you want to create reverse zone for 1.0.10.in-addr.arpa.? [yes]: <Press Enter>
The IPA Master Server will be configured with:
Hostname: ipa.example.com
IP address(es): 10.0.1.10
Domain name: example.com
Realm name: EXAMPLE.COM
BIND DNS server will be configured to serve IPA domain with:
Forwarders: 8.8.8.8, 1.1.1.1
Forward policy: only
Reverse zone(s): 1.0.10.in-addr.arpa.
Continue to configure the system with these values? [no]: yesThe installation takes 5 to 15 minutes depending on your hardware. It configures the 389 Directory Server, MIT Kerberos KDC, Dogtag CA, Apache httpd, BIND DNS (if selected), chronyd, and the IPA client on the server itself. A successful installation ends with output similar to this.
Restarting the KDC
Configuring client side components
This program will set up IPA client.
Version 4.12.2
Using existing certificate '/etc/ipa/ca.crt'.
Client hostname: ipa.example.com
Realm: EXAMPLE.COM
DNS Domain: example.com
IPA Server: ipa.example.com
BaseDN: dc=example,dc=com
Configured sudoers in /etc/nsswitch.conf
Configured /etc/sssd/sssd.conf
Systemwide CA database updated.
Adding SSH public key from /etc/ssh/ssh_host_ed25519_key.pub
Adding SSH public key from /etc/ssh/ssh_host_ecdsa_key.pub
Adding SSH public key from /etc/ssh/ssh_host_rsa_key.pub
SSSD enabled
Configured /etc/openldap/ldap.conf
Configured /etc/ssh/ssh_config
Configured /etc/ssh/sshd_config
Client configuration complete.
The ipa-client-install command was successful
==============================================================================
Setup complete
Next steps:
1. You must make sure these network ports are open:
TCP Ports:
* 80, 443: HTTP/HTTPS
* 389, 636: LDAP/LDAPS
* 88, 464: kerberos
* 53: bind
UDP Ports:
* 88, 464: kerberos
* 53: bind
* 123: ntp
2. You can now obtain a kerberos ticket using the command: 'kinit admin'
This ticket will allow you to use the IPA tools (e.g., ipa user-find)
and the web UI.
==============================================================================If the installation fails, check the log file at /var/log/ipaserver-install.log for details. The most common causes are incorrect hostname resolution, insufficient RAM, or port conflicts with existing services.
Step 5: Configure Firewall Ports for FreeIPA
FreeIPA requires several ports for its services. If firewalld is running, open them using predefined service names.
sudo firewall-cmd --add-service={http,https,dns,ntp,freeipa-ldap,freeipa-ldaps,kerberos,kpasswd} --permanent
sudo firewall-cmd --reloadVerify the services are listed in the active zone.
$ sudo firewall-cmd --list-services
cockpit dhcpv6-client dns freeipa-ldap freeipa-ldaps http https kerberos kpasswd ntp sshHere is a summary of all ports FreeIPA uses.
| Service | Port | Protocol |
|---|---|---|
| HTTP | 80 | TCP |
| HTTPS | 443 | TCP |
| LDAP | 389 | TCP |
| LDAPS | 636 | TCP |
| Kerberos | 88 | TCP/UDP |
| Kpasswd | 464 | TCP/UDP |
| DNS | 53 | TCP/UDP |
| NTP | 123 | UDP |
Step 6: Verify IPA Services and Get a Kerberos Ticket
After installation, verify all FreeIPA services are running.
$ sudo ipactl status
Directory Service: RUNNING
krb5kdc Service: RUNNING
kadmin Service: RUNNING
named Service: RUNNING
httpd Service: RUNNING
ipa-custodia Service: RUNNING
pki-tomcatd Service: RUNNING
ipa-otpd Service: RUNNING
ipa-dnskeysyncd Service: RUNNING
ipa: INFO: The ipactl command was successfulObtain a Kerberos ticket for the admin user. You need this ticket to run any ipa commands.
$ kinit admin
Password for [email protected]:Verify the ticket was issued successfully.
$ klist
Ticket cache: KCM:0:58115
Default principal: [email protected]
Valid starting Expires Service principal
03/19/2026 09:15:22 03/20/2026 09:15:18 krbtgt/[email protected]Set the default login shell to /bin/bash for all new users.
$ ipa config-mod --defaultshell=/bin/bash
Maximum username length: 32
Home directory base: /home
Default shell: /bin/bash
Default users group: ipausers
Default e-mail domain: example.com
Search time limit: 2
Search size limit: 100
User search fields: uid,givenname,sn,telephonenumber,ou,title
Group search fields: cn,description
Enable migration mode: FALSE
Certificate Subject base: O=EXAMPLE.COM
Password Expiration Notification (days): 4
SELinux user map order: guest_u:s0$xguest_u:s0$user_u:s0$staff_u:s0-s0:c0.c1023$sysadm_u:s0-s0:c0.c1023$unconfined_u:s0-s0:c0.c1023
Default SELinux user: unconfined_u:s0-s0:c0.c1023
Default PAC types: MS-PAC, nfs:NONE
IPA masters: ipa.example.com
IPA CA servers: ipa.example.com
IPA CA renewal master: ipa.example.comStep 7: Access the FreeIPA Web UI
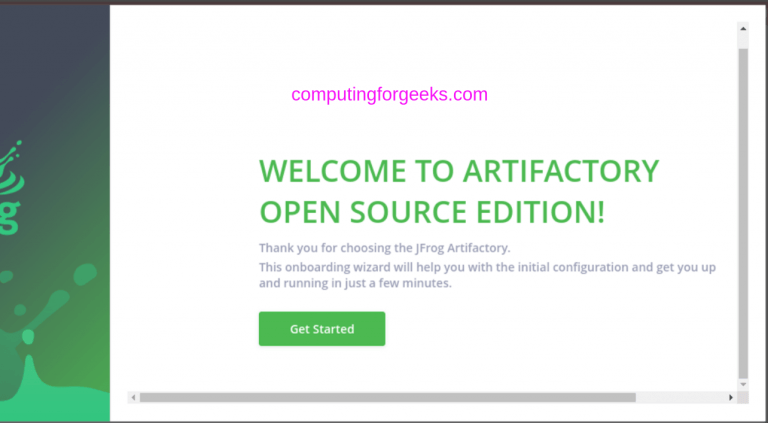
Open a browser and navigate to https://ipa.example.com. The Web UI uses the self-signed CA certificate issued during installation. Accept the certificate warning or import the IPA CA certificate from https://ipa.example.com/ipa/config/ca.crt into your browser trust store.

Log in with the username admin and the IPA admin password you set during installation. After login, the FreeIPA dashboard appears with navigation for Identity, Policy, Authentication, and Network Services.

Step 8: Create Users and Groups
FreeIPA provides both CLI and Web UI for user management. Here we cover the CLI approach, which is faster for bulk operations.
Add a New User
$ ipa user-add jdoe \
--first=John --last=Doe \
[email protected] --password
Password:
Enter Password again to verify:
-------------------
Added user "jdoe"
-------------------
User login: jdoe
First name: John
Last name: Doe
Full name: John Doe
Display name: John Doe
Initials: JD
Home directory: /home/jdoe
GECOS: John Doe
Login shell: /bin/bash
Principal name: [email protected]
Principal alias: [email protected]
User password expiration: 20260319081230Z
Email address: [email protected]
UID: 1201400001
GID: 1201400001
Password: True
Member of groups: ipausers
Kerberos keys available: TrueList Users
Verify the user was created by listing all IPA users.
$ ipa user-find
---------------
2 users matched
---------------
User login: admin
Last name: Administrator
Home directory: /home/admin
Login shell: /bin/bash
Principal alias: [email protected]
UID: 1201400000
GID: 1201400000
Account disabled: False
User login: jdoe
First name: John
Last name: Doe
Home directory: /home/jdoe
Login shell: /bin/bash
Principal name: [email protected]
Principal alias: [email protected]
Email address: [email protected]
UID: 1201400001
GID: 1201400001
Account disabled: False
----------------------------
Number of entries returned 2
----------------------------Create a Group and Add Members
Create a new group for your engineering team.
$ ipa group-add engineering --desc="Engineering team"
------------------------
Added group "engineering"
------------------------
Group name: engineering
Description: Engineering team
GID: 1201400002Add users to the group.
$ ipa group-add-member engineering --users=jdoe
Group name: engineering
Description: Engineering team
GID: 1201400002
Member users: jdoe
-------------------------
Number of members added 1
-------------------------Verify group membership.
$ ipa group-show engineering
Group name: engineering
Description: Engineering team
GID: 1201400002
Member users: jdoeStep 9: Enroll the First FreeIPA Client
A FreeIPA deployment is not complete until clients are enrolled. On a separate Rocky Linux 10, AlmaLinux 10, or RHEL 10 machine, install the FreeIPA client package.
sudo dnf install -y freeipa-clientMake sure the client can resolve the IPA server hostname. If you are not using integrated DNS, add the server to /etc/hosts on the client machine.
echo "10.0.1.10 ipa.example.com ipa" | sudo tee -a /etc/hostsSet the client hostname to an FQDN within the IPA domain.
sudo hostnamectl set-hostname client1.example.comRun the client enrollment. The --mkhomedir flag automatically creates home directories for IPA users on first login.
sudo ipa-client-install --mkhomedir --server=ipa.example.com --domain=example.comThe installer prompts for the IPA admin credentials to authorize enrollment. After completion, test by logging in as the IPA user from the client.
$ ssh [email protected]
Password:
Password expired. Change your password now.
Current Password:
New password:
Retype new password:
Creating home directory for jdoe.
[jdoe@client1 ~]$ id
uid=1201400001(jdoe) gid=1201400001(jdoe) groups=1201400001(jdoe),1201400002(engineering)The user’s first login requires a password change because the initial password was set by an admin. After changing it, the user gets a fully provisioned session with the correct group memberships.
Step 10: Configure Host-Based Access Control (HBAC) Policies
HBAC policies control which users can access which hosts. By default, FreeIPA has an allow_all rule that permits any user to log into any enrolled host. In production, disable this rule and create targeted policies.
Disable the Default allow_all Rule
$ ipa hbacrule-disable allow_all
------------------------------
Disabled HBAC rule "allow_all"
------------------------------Create a New HBAC Rule
Create a rule that allows the engineering group to access client1.example.com via SSH and console.
$ ipa hbacrule-add allow_engineering_client1 --desc="Allow engineering on client1"
--------------------------------------------------
Added HBAC rule "allow_engineering_client1"
--------------------------------------------------
Rule name: allow_engineering_client1
Description: Allow engineering on client1
Enabled: TRUEAdd the user group, host, and services to the rule.
$ ipa hbacrule-add-user allow_engineering_client1 --groups=engineering
Rule name: allow_engineering_client1
Description: Allow engineering on client1
Enabled: TRUE
User Groups: engineering
-------------------------
Number of members added 1
-------------------------Add the target host.
$ ipa hbacrule-add-host allow_engineering_client1 --hosts=client1.example.com
Rule name: allow_engineering_client1
Description: Allow engineering on client1
Enabled: TRUE
Hosts: client1.example.com
-------------------------
Number of members added 1
-------------------------Add the HBAC services (sshd and login for console access).
ipa hbacrule-add-service allow_engineering_client1 --hbacsvcs=sshd
ipa hbacrule-add-service allow_engineering_client1 --hbacsvcs=loginImportant: Keep Admin Access
Before testing, create a rule that allows the admin user to access all hosts. Otherwise you will lock yourself out.
ipa hbacrule-add allow_admin_all --desc="Admin access to all hosts"
ipa hbacrule-add-user allow_admin_all --users=admin
ipa hbacrule-mod allow_admin_all --hostcat=all --servicecat=allTest the HBAC Rule
FreeIPA provides a built-in HBAC test tool.
$ ipa hbactest --user=jdoe --host=client1.example.com --service=sshd
--------------------
Access granted: True
--------------------
Matched rules: allow_engineering_client1Step 11: Configure Sudo Rules
FreeIPA can centrally manage sudo policies so you do not need to edit /etc/sudoers on every host. Create a sudo rule that allows the engineering group to run all commands with sudo on client1.example.com.
Create a Sudo Rule
$ ipa sudorule-add sudo_engineering --desc="Sudo for engineering on client1"
------------------------------------
Added Sudo Rule "sudo_engineering"
------------------------------------
Rule name: sudo_engineering
Description: Sudo for engineering on client1
Enabled: TRUEAdd the user group, host, and the ALL sudo command group.
ipa sudorule-add-user sudo_engineering --groups=engineering
ipa sudorule-add-host sudo_engineering --hosts=client1.example.com
ipa sudorule-mod sudo_engineering --cmdcat=allCreate a Restricted Sudo Rule
For more restricted access, specify individual commands instead of using --cmdcat=all. First, add a sudo command.
$ ipa sudocmd-add /usr/bin/systemctl
--------------------------------------
Added Sudo Command "/usr/bin/systemctl"
--------------------------------------
Sudo Command: /usr/bin/systemctlCreate a rule that only allows systemctl.
ipa sudorule-add sudo_ops_systemctl --desc="Ops can run systemctl"
ipa sudorule-add-user sudo_ops_systemctl --groups=engineering
ipa sudorule-add-host sudo_ops_systemctl --hosts=client1.example.com
ipa sudorule-add-allow-command sudo_ops_systemctl --sudocmds=/usr/bin/systemctlVerify Sudo Configuration on the Client
On the enrolled client, verify the sudo rules are available. SSSD caches sudo rules from IPA.
$ sudo sssctl sudo-rules jdoe
Rule: sudo_engineering
MatchedThe user can now run sudo commands on the enrolled client based on the centrally managed rules.
Step 12: SELinux Considerations
FreeIPA 4.12 on RHEL 10 and derivatives works correctly with SELinux in enforcing mode. Keep SELinux enforcing in production. If you encounter issues, check the audit log for denials instead of disabling SELinux entirely.
sudo ausearch -m avc -ts recent
sudo sealert -a /var/log/audit/audit.logIf you need to check or set the current SELinux mode, run the following.
$ getenforce
EnforcingUninstalling FreeIPA Server
To remove FreeIPA and revert all configuration changes, run the uninstall command. This is destructive and removes all data in the directory and CA.
$ sudo ipa-server-install --uninstall
This is a NON REVERSIBLE operation and will delete all data and configuration!
It is highly recommended to take a backup of existing data and configuration
using ipa-backup utility before proceeding.
Are you sure you want to continue with the uninstall procedure? [no]: yesConclusion
You now have a fully functional FreeIPA Server running on Rocky Linux 10, AlmaLinux 10, or RHEL 10 with user management, group policies, HBAC rules, and centralized sudo. For production deployments, set up FreeIPA replication for high availability, configure regular backups with ipa-backup, and consider using Let’s Encrypt SSL certificates for the Web UI if the server is publicly accessible.



![Install Kali Linux 2026.1 Step by Step [Full Guide] 5 Install Kali Linux 2026.1 Step by Step [Full Guide]](https://computingforgeeks.com/wp-content/uploads/2026/03/install-kali-linux-20261-step-by-step-768x403.png)