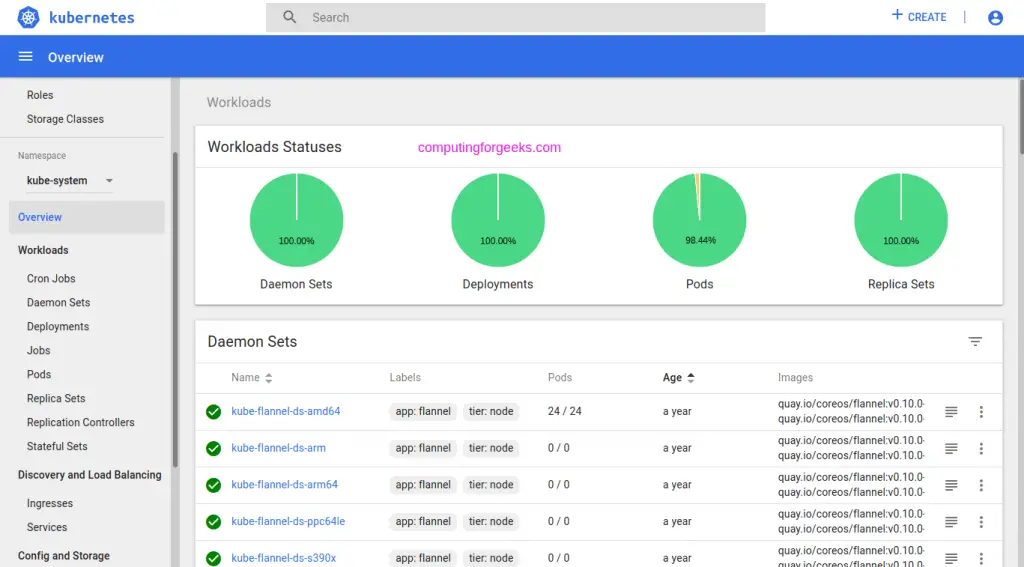
Kubernetes dashboard is a web based user interface for deploying containerized applications to a Kubernetes cluster – Deployments, Jobs, StatefulSets, DaemonSets e.t.c, and managing cluster resources while being able to troubleshoot issues that may arise. You can use the Dashboard to get an overview of applications running on your cluster.
Check our guide below on how to deploy Kubernetes dashboard:
This guide will discuss how you can create an admin user who has access to all Kubernetes resources. The admin user can modify objects in all namespaces as well as administer any other components in a cluster.
Create Admin service account
Let’s start by creating a Service Account manifest file. I’ll name the service account k8sadmin:
$ vim admin-sa.yml
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: k8sadmin
namespace: kube-systemWhere k8sadmin is the name of the service account to be created.
After creating a file, apply the manifest to create objects in your kubernetes cluster.
$ kubectl apply -f admin-sa.yml
serviceaccount/k8sadmin created
clusterrolebinding.rbac.authorization.k8s.io/k8sadmin createdCreate a Cluster Role Binding
Next is to assign the service account created a cluster role binding of cluster-admin.
$ vim admin-rbac.yml
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
namespace: kube-system
name: k8sadmin
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-admin
subjects:
- kind: ServiceAccount
name: k8sadmin
namespace: kube-systemReplace k8sadmin with the name of the service account you created in step 1.
Apply the file.
kubectl apply -f admin-rbac.ymlObtain admin user token
Kubernetes <=1.23.
You can print the generated token for a service account by using the kubectl command.
Set a variable to store the name of the service account.
SA_NAME="k8sadmin"Then run the command below to print the token for the admin user created.
kubectl -n kube-system describe secret $(kubectl -n kube-system get secret | grep ${SA_NAME} | awk '{print $1}')Output:
Name: k8sadmin-token-mm9jd
Namespace: kube-system
Labels: <none>
Annotations: kubernetes.io/service-account.name: k8sadmin
kubernetes.io/service-account.uid: 80fade4b-4270-11ea-9fe4-005056ba45bd
Type: kubernetes.io/service-account-token
Data
====
token: eyJhbGciOiJSUzI1NiIsImtpZCI9IiJ9.eyJpc7MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJrdWJlLXN5c3RlbSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VjcmV0Lm5hbWUxOiJqa211dGFpLWFkbWluLXRva2VuLW1tOWpkIiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZXJ2aWNlLWFjY291bnQubmFtZSI6ImprbXV0YWktYWRtaW4iLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC51aWQiOiI4MGZhZGU0Yi00MjcwLTExZWEtOWZlNC0wMDUwNTZiYTQ1YmQiLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6a3ViZS1zeXN0ZW06amttdXRhaS1hZG1pbiJ9.uMC2ydeHF4jVA5tnKFbBeHRvc4NWqL920jigk2FDeduUdBuFhsNyDcscmL-pBbWHG5KKwOAEuAAeyNaknaHsDadNnbLpp4AMZTTdr22FEp-_v7MfIEQm3QWmq-c0ykpdrzUzGmk5Q3JIpfqeorDI0lZd52-DF4IVMw3VtTNp6ZMHdieQUNRnCEyfs98raCTRAotiXZQaMvmRW5s9peu5hfxM71jufg-Qzmflr9nO-dY2dOHh1WZcKhJqfNfB73GYX2TQlUlurV4Oy0-2CpUUpJ1HAjcSHzKGuSrMUAMAhRwhbZZXhwvbQ6Ei_9Vv2PkD8_Pw9c-k9x-bblFSAqyFhA
ca.crt: 1025 bytes
namespace: 11 bytesCopy the contents in token key.
Kubernetes >=1.24
From Kubernetes 1.24 on, the token is not automatically created anymore. We’ll instead use TokenRequest API to create tokens.
kubectl create token k8sadminSample output:
eyJhbGciOiJSUzI1NiIsImtpZCI6ImkyWUh6N01DaW9OUG40Uzk0NVVRdlZoZWV0TzQ5cTNOd21UcFQxdE5ud0UifQ.eyJhdWQiOlsiaHR0cHM6Ly9rdWJlcm5ldGVzLmRlZmF1bHQuc3ZjLms4cy5jbG91ZGxhYnNrZS5pbyJdLCJleHAiOjE2Nzg0NTY3MjEsImlhdCI6MTY3ODQ1MzEyMSwiaXNzIjoiaHR0cHM6Ly9rdWJlcm5ldGVzLmRlZmF1bHQuc3ZjLms4cy5jbG91ZGxhYnNrZS5pbyIsImt1YmVybmV0ZXMuaW8iOnsibmFtZXNwYWNlIjoia3ViZS1zeXN0ZW0iLCJzZXJ2aWNlYWNjb3VudCI6eyJuYW1lIjoiamttdXRhaS1hZG1pbiIsInVpZCI6IjQxNGEzMDZkLTU3MjgtNGE3ZS1iZjhhLTdlNjZjNzc0M2I4OSJ9fSwibmJmIjoxNjc4NDUzMTIxLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6a3ViZS1zeXN0ZW06amttdXRhaS1hZG1pbiJ9.MnKpsXpj2xQcqJtx-KTrqpTnQ3l79jhjdHEjtSHvjV4F-Fkvj3YpqqfqQHmN5_WNKxrgxQNdbUEVLjBJmhYYrZEOiGRdtb7s5XKA6C4eY-mGr59UZvdNWyILHfoDCi8YT8IyUdu6wpAO_6zdHHh95F2g7mM0QZAgVHT5RR3hPCDRrUpYm1ZiDUohg-A6RnnSoDXKpHQ4Y9v_HQZWufdldfQ0XYwI47nDnKkimLyTcn-n9hWMBbUh6x79paL0Jf0QfBoFRtrzWlDMhyhPPxEehgwo8Qdmplz1vA6trBUl52gEz0E9iVyGsMz3bKhbk_-F-raTYhHlJx2iqdmnnON0uwTo create a secret create a file.
$ vim k8sadmin-secret.yaml
apiVersion: v1
kind: Secret
metadata:
name: k8sadmin-token
annotations:
kubernetes.io/service-account.name: k8sadmin
type: kubernetes.io/service-account-tokenCreate object in kubernetes
kubectl apply -f k8sadmin-secret.yamlYou can then print the token.
export NAMESPACE="kube-system"
export K8S_USER="k8sadmin"
kubectl -n ${NAMESPACE} describe secret $(kubectl -n ${NAMESPACE} get secret | (grep ${K8S_USER} || echo "$_") | awk '{print $1}') | grep token: | awk '{print $2}'\nAccessing Kubernetes Dashboard
Once the token is created, you can access your Kubernetes Dashboard with it. If using the NodePort to access dashboard service, you can obtain port allocated by issuing the command.
$ kubectl get services -n <namespace> | grep dashboard
kubernetes-dashboard NodePort 10.111.76.69 <none> 443:32254/TCP 414dFor me I will access the Kubernetes dashboard on any cluster machine IP address on port 32254.

Select Token authentication type and paste your token to access the dashboard.
Creating non admin user account
We created an admin user account which has full access to cluster resources. If you would like to grant users access with limit to the namespace, refer to our previous guide below.
More guides on Kubernetes and containers:
