What’s netfilter and iptables?
Netfilter is a framework provided by Linux that allows various networking-related operations to be implemented in the form of customized handlers. Iptables is a widely used firewall tool that interfaces with the kernel’s netfilter packet filtering framework.

The iptables firewall works by interacting with the packet filtering hooks in the Linux kernel’s networking stack. These kernel hooks are known as the netfilter framework.
Disable netfilter on a KVM bridge
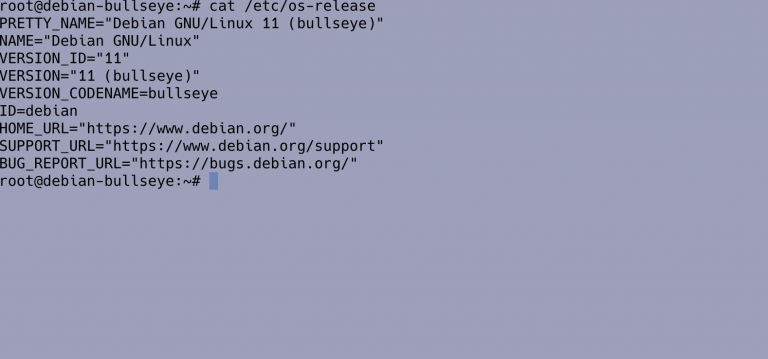
In order to prevent bridged traffic from getting pushed through the host’s iptables rules, you need to set kernel settings in the /proc/sys/ directory. This can be a run-time change or persistent.
For a quick overview of all settings configurable in the /proc/sys/ directory, type the command:
sudo sysctl -a
The sysctl command can be used in place of echo to assign values to writable files in the /proc/sys/ directory. So let’s disable netfilter on KVM bridge, for runtime change, run:
echo 0 | sudo tee /proc/sys/net/bridge/bridge-nf-call-arptables echo 0 | sudo tee /proc/sys/net/bridge/bridge-nf-call-iptables echo 0 | sudo tee /proc/sys/net/bridge/bridge-nf-call-ip6tables
Note that these special settings within /proc/sys/ are lost when the machine is rebooted. To preserve custom settings, add them to the /etc/sysctl.conf file.
sudo tee -a /etc/sysctl.conf <<EOF net.bridge.bridge-nf-call-ip6tables = 0 net.bridge.bridge-nf-call-iptables = 0 net.bridge.bridge-nf-call-arptables = 0 EOF
Reload:
sudo sysctl -p /etc/sysctl.confEach time the system boots, the init program runs the /etc/rc.d/rc.sysinit script which contains a command to execute sysctl using /etc/sysctl.conf to determine the values passed to the kernel.
With this set, you’re good to go. Test your bridge connectivity if it’s working now.
Check more guides on KVM:




Thank you for this post! Saved me some hours to fix a home-assistant vm running in virt-manager (kvm) on a Ubuntu host. First ‘solution’ was to remove the br_netfilter module, but that is re-activated on reboot. This solution feels far more solid.
We have several VMs that have suddenly become completely encapsulated, with nothing coming out beyond the VM’s internal switch. With no apparent changes and affecting several Windows and Linux systems, allow me to question the reliability of KVM at this time.