What is SSL Certificate? SSL stands for secure socket layer. It is a standard global technology which ensures data encryption between a web server and a web client, minimizing the risks of websites and web applications being hacked. An SSL certificate installed on a web server ensures this secure connection. An SSL certificate contains a website public key, website identity and any other related information and hosted in the website original server. Any client trying to communicate with the original server needs to reference the file to obtain the website public key and identity.
Let’s Encrypt is a Certificate Authority providing an easy way to acquire and install free SSL/ TLS certificates, enabling encrypted http traffic on web servers. It provides a software client called certbot that make SSL installation easy by having most steps of installation automated. For Apache and Nginx web servers, SSL installation is fully automated. In this guide, we are going to look at how to use Let’s Encrypt Wildcard SSL Certificate with Nginx and Apache on Ubuntu / CentOS.
Install Certbot on Ubuntu | CentOS
To install certbot on Ubuntu and CentOS we are going to run the command as shown below depending on the web server we are using.
For Nginx Web Server
To install certbot for Nginx, use the following commands:
### Ubuntu / Debian ###
sudo apt install certbot python3-certbot-nginx
### CentOS 8 / CentOS Stream 8 / Rocky Linux 8 / AlmaLinux 8 ###
sudo yum -y install epel-release
sudo dnf config-manager --set-enabled powertools
sudo yum -y install certbot python3-certbot-nginx nginx
### CentOS 7 ###
sudo yum -y install epel-release
sudo yum -y install certbot python2-certbot-nginx nginxFor Apache Web Server
For Apache web server, run the below command to install certbot:
### Ubuntu / Debian ###
sudo apt install certbot python3-certbot-apache2
### CentOS 8 / CentOS Stream 8 / Rocky Linux 8 / AlmaLinux 8 ###
sudo yum -y install epel-release
sudo dnf config-manager --set-enabled powertools
sudo yum -y install certbot python3-certbot-apache httpd
### CentOS 7 ###
sudo yum -y install epel-release
sudo yum -y install certbot python2-certbot-apache httpdCheck Nginx and Apache configurations
We need to ensure that we have the web server virtual hosts after our preferred web server. The file should contain web server name and alias as shown.
For Apache, check the file as shown:
### Ubuntu / Debian ###
sudo vim /etc/apache2/sites-available/example.com.conf
### CentOS / Rocky Linux / AlmaLinux ###
sudo vim /etc/httpd/conf.d/example.com.confYou should have your server name and alias name as shown:
ServerName example.com
ServerAlias www.example.comThe same case for Nginx, check the configuration as shown:
sudo vim /etc/nginx/conf.d/example.com.confYou should have the server name and alias here as well.
server_name example.com www.example.com;Generating Let’s Encrypt Wildcard SSL using Certbot
Having confirmed the webserver virtual hosts, it is time to request for Let’s Encrypt wildcard SSL. A wildcard SSL is a type of SSL that covers the main domain and all its subdomains. For example, a wildcard ssl for *.example.com should also protect something.example.com, one.example.com and so on.
Run the command as shown below to request SSL for *.example.com.
sudo certbot certonly \
--agree-tos \
--email [email protected] \
--manual \
--preferred-challenges=dns \
- d example.com \
-d *.example.com \
--server https://acme-v02.api.letsencrypt.org/directoryBelow is a description of the various parameters used in the above command:
- –certonly: The certonly option in our command will make sure that we just want to issue SSL certificate. If you remove the certonly option from the command, Certbot will issue the SSL certificate and it will also update your virtual host file to apply the SSL certificate.
- –agree-tos: Used to agree Let’s Encrypt terms of service.
- –email: The email is provided for storing the SSL in Let’s Encrypt account. It will be used in notifying us when the SSL is about to expire.
- –manual: This brings an interactive way of issuing the SSL where we are prompted for more information.
- –preferred-challenges: Specifies the method of SSL verification. The domain name has to be verified before issuing SSL. In this case we are slecting DNS
- -d: Used to specify the domains to issue SSL certificate
- –server: Used to specify the API endpoint to issue SSL certificate.
Once you execute the command, you will receive a TXT record which you need to add to your DNS server. The records will look as below:
Please deploy a DNS TXT record under the name
_acme-challenge.example.com with the following value:
HejzlvXokaKoAq_xnr5LTplWbKYNScVH-ASy1vMYMGE
Before continuing, verify the record is deployed.
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Press Enter to ContinueAdd the records to your DNS server for the webserver domain.
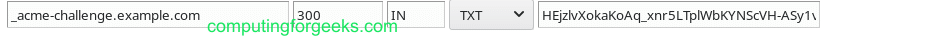
Confirm the record is available in your DNS server.

Once you have verified that the record has been deployed, press Enter to obtain the SSL. You should get feedback as below:
IMPORTANT NOTES:
- Congratulations! Your certificate and chain have been saved at:
/etc/letsencrypt/live/example.com/fullchain.pem
Your key file has been saved at:
/etc/letsencrypt/live/example.com/privkey.pem
Your cert will expire on 2020-10-28. To obtain a new or tweaked
version of this certificate in the future, simply run certbot
again. To non-interactively renew *all* of your certificates, run
"certbot renew"
- If you like Certbot, please consider supporting our work by:
Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate
Donating to EFF: https://eff.org/donate-le
Configuring Nginx to use Let’s Encrypt Wildcard SSL
Now configure Nginx web server to use Let’s Encrypt wildcard ssl
We need to edit nginx virtual host configuration file and enable https as below:
sudo vim /etc/nginx/conf.d/example.com.confYour content should now appear as below:
server {
listen 80;
listen [::]:80;
server_name *.example.com;
return 301 https://$host$request_uri;
}
server {
listen 443 ssl;
server_name *.example.com;
ssl_certificate /etc/letsencrypt/live/example.com/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/example.com/privkey.pem;
include /etc/letsencrypt/options-ssl-nginx.conf;
ssl_dhparam /etc/letsencrypt/ssl-dhparams.pem;
root /var/www/example.com;
index index.html;
location / {
try_files $uri $uri/ =404;
}
}Let us enable the file through creating a link to sites-enabled where Nginx reads from during startup.
sudo ln -s /etc/nginx/sites-available/example.com.conf /etc/nginx/sites-enabled/Now test your Nginx configuration to ensure that all settings are okay.
sudo nginx -tYou should get an output as below if nginx configuration is ok.
nginx: the configuration file /etc/nginx/nginx.conf syntax is ok
nginx: configuration file /etc/nginx/nginx.conf test is successfulAfter that reload Nginx.
sudo systemctl restart nginxConfiguring Apache to use Let’s Encrypt wildcard SSL
For Apache webserver, repeat the same procedure as for Nginx. The config file edit for Apache is:
sudo vim /etc/apache2/sites-available/api.example.com.confHave SSL lines like below.
SSLCertificateFile /etc/letsencrypt/live/example.com/cert.pem
SSLCertificateKeyFile /etc/letsencrypt/live/example.com/privkey.pem
SSLCertificateChainFile /etc/letsencrypt/live/example.com/fullchain.pemWhen done, reload Apache
sudo systemctl restart apache2That’s it. Your webserver is now set up to serve wildcard subdomains. You can test SSL from the browswer and you should be able to get Let’s Encrypt SSL information as below:

Enjoy developing and check more captivating Linux guides below:



![Install Kali Linux 2026.1 Step by Step [Full Guide] 6 Install Kali Linux 2026.1 Step by Step [Full Guide]](https://computingforgeeks.com/wp-content/uploads/2026/03/install-kali-linux-20261-step-by-step-768x403.png)

I’m sure this method works fine, but it doesn’t describe auto renewal, which via this method requires a script that can access your DNS providers records and update the TXT value every renewal.
This is only really a guide for getting a single cert, that must be manually followed whenever it expires
Hi Sam,
You can try a cron job
# Ubuntu / Debian
/usr/local/bin/certbot renew –pre-hook “systemctl stop apache2” –post-hook “systemctl start apache2”
# CentOS / Fedora
/usr/local/bin/certbot renew –pre-hook “systemctl stop httpd” –post-hook “systemctl start httpd”
Nice tutorial, I went through the steps and got all the way through but it did not create a ssl conf file in my sites-enabled. Any idea how to get that to happen?
Any error message?
Wildcard does not work for non-www domain. so add the domain extra. -d *.brutalrace.fr -d brutalrace.fr
Sure thanks for the comment. We’re updating the article now.