Starting as a fork of pfSense® and m0n0wall in the year 2014, OPNSense has its official release in January 2015. It is an open source, easy-to-use, and easy-to-build Hardened BSD based firewall and routing platform.
OPNSense contains most of the features you will find inexpensive commercial firewalls out there plus more. Even though the project has quickly evolved, it has as much as possible retained familiar aspects of both m0n0wall and pfSense. What motivates the project is its strong focus on security and code quality.
From OPNSense website, the following are the core Features that the firewall proffers:
OPNsense Core Features
- Traffic Shaper
- Two-factor Authentication throughout the system
- Captive portal
- Forward Caching Proxy (transparent) with Blacklist support
- Virtual Private Network (site to site & road warrior, IPsec, OpenVPN & legacy PPTP support)
- High Availability & Hardware Failover ( with configuration synchronization & synchronized state tables)
- Intrusion Detection and Prevention
- Build-in reporting and monitoring tools including RRD Graphs
- Netflow Exporter
- Network Flow Monitoring
- Support for plugins
- DNS Server & DNS Forwarder
- DHCP Server and Relay
- Dynamic DNS
- Encrypted configuration backup to Google Drive
- Stateful inspection firewall
- Granular control over state table
- 802.1Q VLAN support
“Take someone who doesn’t keep score, who’s not looking to be richer, or afraid of losing, who has not the slightest interest even in his own personality: he’s free.”
—Jalāl ad-Dīn Muhammad Rūmī
Step 1: Download OPNServer
Go over to OPNServer Download page and grab your copy there. Choose your architecture, Image type e.g ISO and a Mirror close to you for faster download.
After your OPNServer File is downloaded, please proceed and decompress it using bunzip2 as shown below.
bunzip2 -d OPNsense-<version>-OpenSSL-dvd-amd64.iso.bz2 Your ISO file should be ready after this.
Step 2: Installation of OPNSense
You can install OPNServer on a dedicated server or in a Virtual Machine environment. You will need at least two network interfaces. One for LAN connection, and another one for WAN.
OPNSense installation will begin after you boot off ISO image. On the first window, select the installation type.

Click “Ok, let’s go” to start the installation of OPNSense.

Pick installation type. Use “Guided Installation” for easy setup or manual for advanced installation. The other options apply for existing installation.

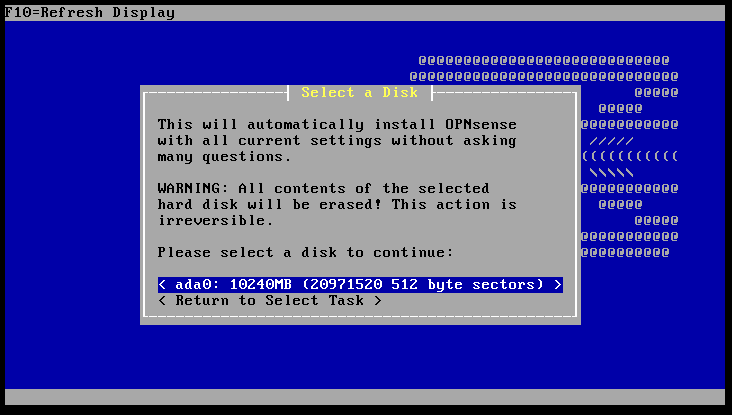
Select the disk where OPNSense will be installed.
Wait for the installation to finish.

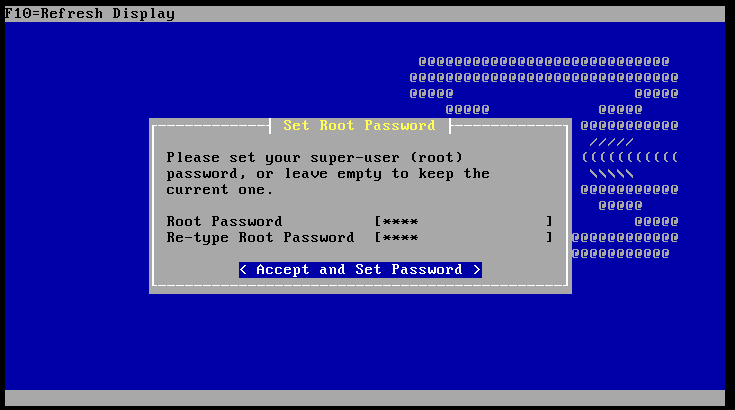
Set root password OPNSense firewall appliance.
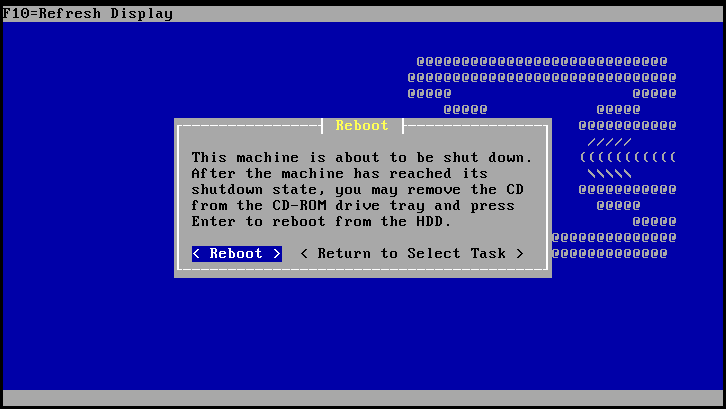
Once the installation is complete, reboot the server to start OPNSense configuration.
After it reboots, login with username root and password opnsense

Step 3: OPNSense Assigning Interfaces
After OPNSense reboots, you will be presented with an “Options” page as pictured below where you can begin your configurations.
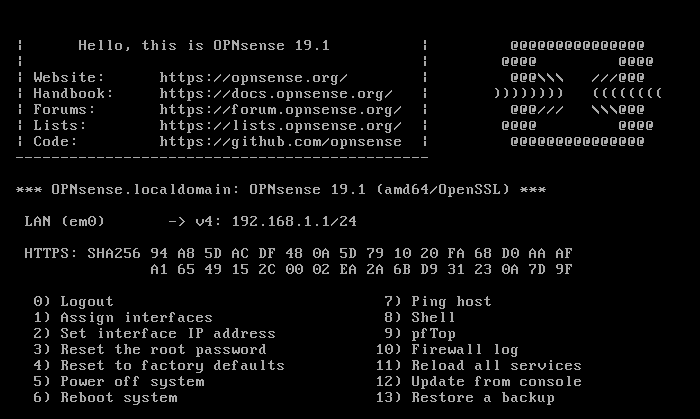
We are going to assign interfaces as option 1

em0 is the default interfaces in OPNSense and after it is assigned as WAN, you can proceed to Set interface IP Address (option 2). You can choose dhcp or you can enter the IP Manually

Do the same for the second interface.
Step 4: Launch OPNSense WebGUI
When you have been assigned with an IP or you manually set ip up, you can proceed o launch OPNSense Web GUI using the IP address:
http://ip-address
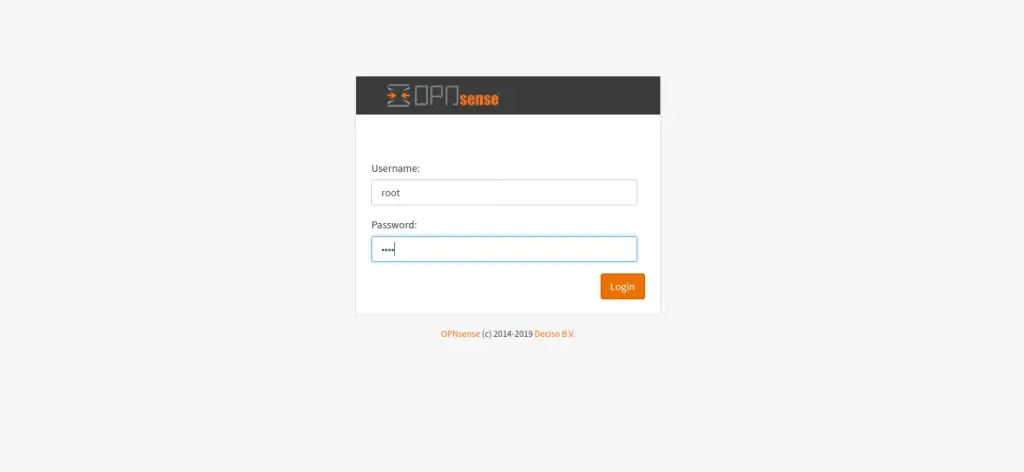
Enter username as root and password as the one you set up during installation.
Step 5: Initial OPNSense Configuration

After logging into the Web interface, you now have the freedom to do any configuration you would wish to implement. All the way from Firewalls, VPN, Security and much more. You can go over to their Documentation page and explore your way in and out.
Thank you guys for reading through. In our next guides, we will cover different configuration options for OPNSense. Stay connected by subscribing to our newsletter for updates. Until then, check other firewall related guides available on our blog.