We recently covered the installation of FreeIPA Server on Ubuntu server. In this guide, I’ll show you how you can install and configure FreeIPA Client on Ubuntu 22.04/20.04/18.04/16.04 and CentOS 7 Linux system. FreeIPA is an open source Identity management system sponsored by Red Hat. It aims to provide an easily managed Identity, Policy, and Audit.
For Vanilla LDAP, use: How to configure LDAP Client on Ubuntu
Setup Prerequisite:
- Install FreeIPA Server
- Installed and updated Ubuntu / CentOS 7
- Root access
If you don’t have FreeIPA server ready, check:
Once the installation of FreeIPA Server is complete, setup FreeIPA Client using steps covered here.
Step 1: Update system
We always start server configurations by doing an update of system packages:
Ubuntu:
sudo apt update && sudo apt -y full-upgrade
[ -f /var/run/reboot-required ] && sudo reboot -fCentOS:
Update CentOS with the following commands:
sudo yum -y updateIf you get kernel updates, consider rebooting the server for changes to take place.
Configure valid client hostname (FQDN) :
sudo hostnamectl set-hostname node-01.computingforgeeks.comStep 2: Install FreeIPA Client
FreeIPA client is available on repositories for Ubuntu / CentOS Linux. Install it using the command:
Ubuntu:
Below are the commands you’ll use to install FreeIPA Client on Ubuntu system.
sudo apt install freeipa-clientCentOS 7:
Install FreeIPA Client on CentOS 7 with the command below.
sudo yum -y install ipa-client When prompted to provide a Kerberos realm for the server, just skip by pressing <Enter> key.

Install FreeIPA Client on CentOS 7
Run the command below to install FreeIPA Client on CentOS 7.
sudo yum install ipa-clientThis will be configured in the next step:
Step 3: Configure FreeIPA Client
Once the installation of client package is complete. Add hostname and IP address of your IPA Server to /etc/hosts file:
$ sudo vim /etc/hosts
# Add FreeIPA Server IP and hostname
192.168.58.121 ipa.computingforgeeks.com ipaReplace:
- 192.168.58.121 IP address of your FreeIPA replica or master server.
- ipa.computingforgeeks.com with its hostname:
Then configure IPA client on this server so that users can start authenticating against it:
$ sudo ipa-client-install --hostname=`hostname -f` \
--mkhomedir \
--server=ipa.computingforgeeks.com \
--domain computingforgeeks.com \
--realm COMPUTINGFORGEEKS.COM
Autodiscovery of servers for failover cannot work with this configuration.
If you proceed with the installation, services will be configured to always access the discovered server for all operations and will not fail over to other servers in case of failure.
Proceed with fixed values and no DNS discovery? [no]: yes
Client hostname: node-01.computingforgeeks.com
Realm: COMPUTINGFORGEEKS.COM
DNS Domain: computingforgeeks.com
IPA Server: ipa.computingforgeeks.com
BaseDN: dc=computingforgeeks,dc=comThis will start configuring FreeIPA Client on your server:
Synchronizing time
No SRV records of NTP servers found and no NTP server or pool address was provided.
Using default chrony configuration.
Attempting to sync time with chronyc.
Time synchronization was successful.
User authorized to enroll computers: admin
Password for [email protected]:
Successfully retrieved CA cert
Subject: CN=Certificate Authority,O=COMPUTINGFORGEEKS.COM
Issuer: CN=Certificate Authority,O=COMPUTINGFORGEEKS.COM
Valid From: 2018-06-30 08:27:06
Valid Until: 2038-06-30 08:27:06
Enrolled in IPA realm COMPUTINGFORGEEKS.COM
Created /etc/ipa/default.conf
New SSSD config will be created
Configured sudoers in /etc/nsswitch.conf
Configured /etc/sssd/sssd.conf
Configured /etc/krb5.conf for IPA realm COMPUTINGFORGEEKS.COM
trying https://ipa.computingforgeeks.com/ipa/json
.......................If everything went as expected, you should get a successful message like below:
The ipa-client-install command was successfulStep 4: Enable mkhomedir ( For Ubuntu only)
By default, sssd service will not create a home directory for the user on the first login, we need to enable this feature by modifying PAM configuration file.
sudo bash -c "cat > /usr/share/pam-configs/mkhomedir" <<EOF
Name: activate mkhomedir
Default: yes
Priority: 900
Session-Type: Additional
Session:
required pam_mkhomedir.so umask=0022 skel=/etc/skel
EOFThen run:
sudo pam-auth-updateSelect <OK>

Ensure “activate mkhomedir” is selected, it should have [*]

Then Select <Ok> to save changes.
Step 4: Testing FreeIPA Client
Now that we have everything we need to be configured, let’ create test user account on FreeIPA Server and try ssh to the client with the added user account. You can add an account to FreeIPA server from UI or CLI
Add user account from CLI:
Login to FreeIPA server and get a Kerberos ticket for admin user:
$ kinit admin
Password for [email protected]:Enter admin password when prompted. Confirm that you have an active ticket using the command:
$ klist
Ticket cache: KEYRING:persistent:0:0
Default principal: [email protected]
Valid starting Expires Service principal
06/30/2018 09:33:40 07/01/2018 09:33:37 krbtgt/[email protected]Add user to FreeIPA:
- Set default shell to /bin/bash for all accounts:
sudo ipa config-mod --defaultshell=/bin/bash- Create user
$ ipa user-add jmutai --first=Josphat \
--last=Mutai --email=[email protected] --password
Password:
Enter Password again to verify:
-------------------
Added user "jmutai"
-------------------
User login: jmutai
First name: Josphat
Last name: Mutai
Full name: Josphat Mutai
Display name: Josphat Mutai
Initials: JM
Home directory: /home/jmutai
GECOS: Josphat Mutai
Login shell: /bin/bash
Principal name: [email protected]
Principal alias: [email protected]
Email address: [email protected]
UID: 32200001
GID: 32200001
Password: True
Member of groups: ipausers
Kerberos keys available: TrueLogin to enrolled client and check user existence:
root@node-01:~# id jmutai
uid=32200001(jmutai) gid=32200001(jmutai) groups=32200001(jmutai)You can confirm the existence of a user with ID 32200001
root@node-01:~# ssh jmutai@localhost
The authenticity of host 'localhost (<no hostip for proxy command>)' can't be established.
ECDSA key fingerprint is SHA256:y4GzK0NLDHF+g8pKNstpPq0Z6Gui+4jq/0WjtqKf5CE.
Are you sure you want to continue connecting (yes/no)? yes
Password:
Password expired. Change your password now.
Current Password:
New password:
Retype new password:
Creating directory '/home/jmutai'.
Welcome to Ubuntu 18.04 LTS (GNU/Linux 4.15.0-23-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Sat Jun 30 10:04:49 UTC 2018
jmutai@node-01:~$ id
uid=32200001(jmutai) gid=32200001(jmutai) groups=32200001(jmutai)Add the user account to FreeIPA from UI:
To add an account on Web UI, login to FreeIPA web interface and navigate to:
Identity > Users > Active users > Add
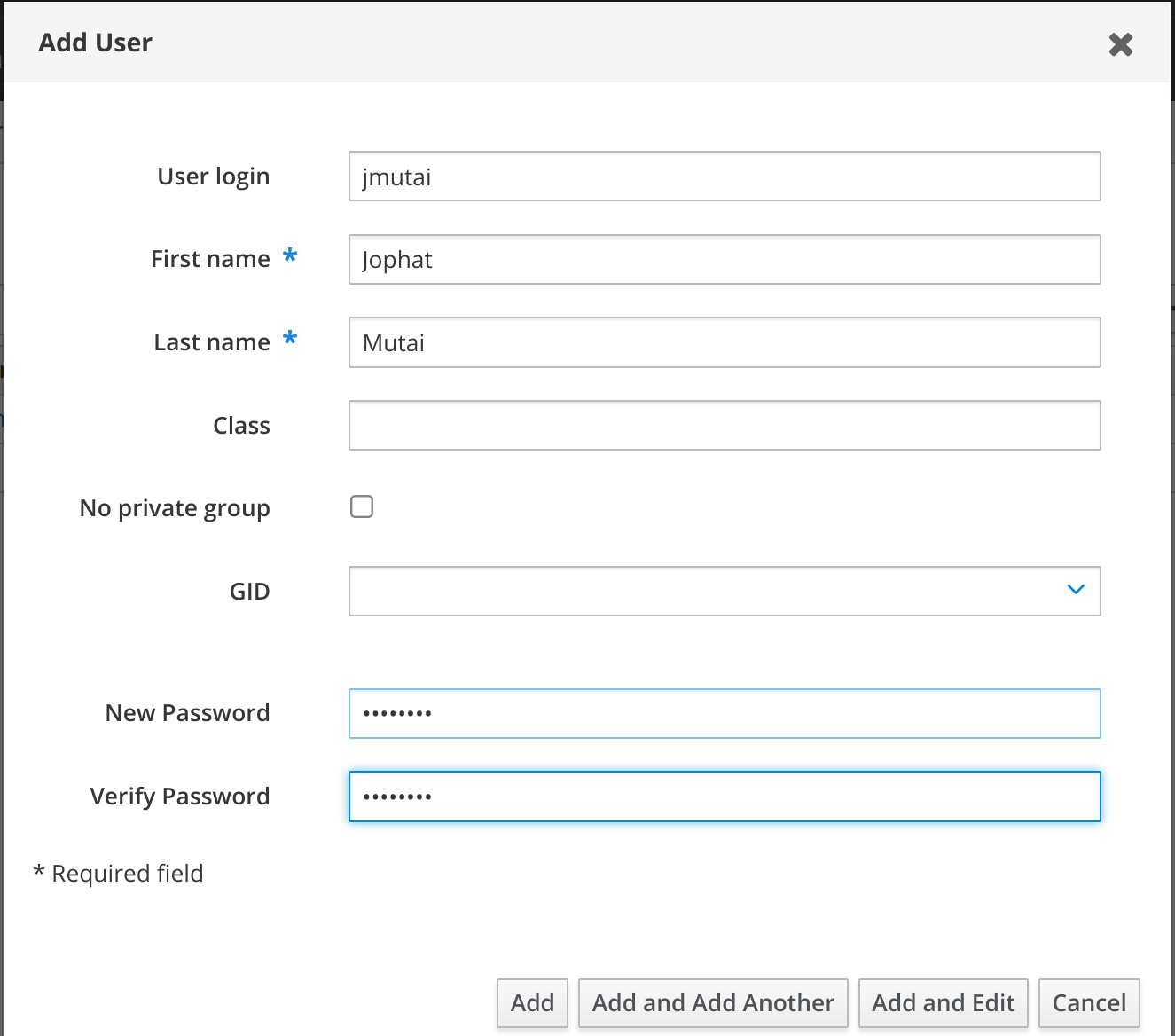
Click Add button to add the user.
Enable Passwordless Authentication using Private Key
If you would like to authenticate to a server without a password, copy your Public key to FreeIPA Server:


Click the Add button under “SSH public keys“, paste your public key into the box and save.
Related guides:
