The Harbor Registry is an enterprise-class image and helm registry server that stores and distributes container images and helm charts. With Harbor you can store and manage images for use with your Kubernetes, OpenShift and any other internal container orchestration platform. In this guide, we will explore how one can configure Active Directory user authentication on Harbor registry.
For Linux LDAP / FreeIPA, refer to:
Setup Pre-requisites
You’re expected to have a running Harbor image registry in the cloud or in your internal infrastructure. Refer to our guides below on the installation of Harbor image registry:
- Install Harbor Image Registry on Kubernetes / OpenShift with Helm Chart
- Install Harbor Container Image Registry on CentOS / Debian / Ubuntu
The recommended deployment method is on Kubernetes or OpenShift using Helm chart. I hope official operator will come out soon.
Integrate Active Directory with Harbor Registry
On the Active Directory end, you should at minimum have:
- User for Binding to Active Directory – Username and Password
- A group for Harbor users
- A Base DN for your Active Directory
So my sample configuration will be like this:
- LDAP URL: ldap://example.net:389
- Bind User DN: cn=HarborAdmin,ou=BindUsers,dc=example,dc=net
- Bind User Password: StronADUserPasss
- Base DN: OU=CompanyUsers,DC=example,DC=net
- LDAP UID: sAMAccountName
- LDAP Scope: Subtree
- LDAP Group Membership DN: CN=HarborUsers,OU=CompanyGroups,DC=example,DC=net
You’ll have to get correct values from your Active Directory and replace accordingly.
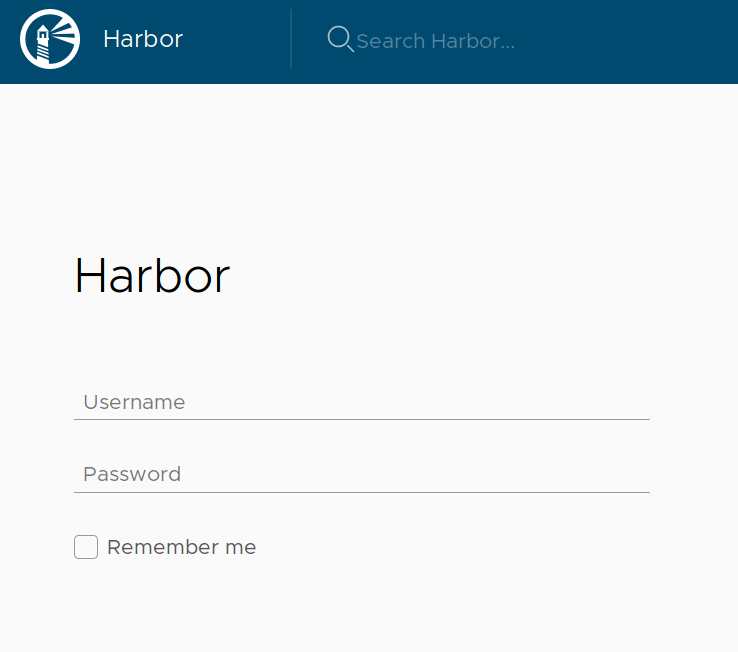
Step 1: Login to harbor dashboard
Login to your Harbor registry dashboard as admin user.
Step 2: Configure LDAP Authentication for AD
Then navigate to Administration > Configuration > Authentication
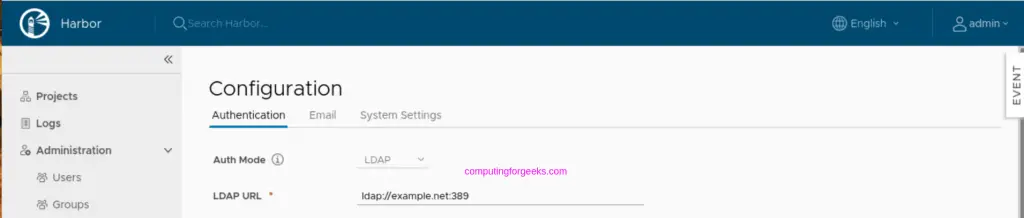
Input your parameters. In my case these are:
Auth Mode: LDAP
LDAP URL: ldap://example.net:389
LDAP Search DN: cn=HarborAdmin,ou=BindUsers,dc=example,dc=net
LDAP Search Password: StronADUserPasss
LDAP Base DN: OU=CompanyUsers,DC=example,DC=net
LDAP UID: sAMAccountName
LDAP Scope: Subtree
LDAP Group Membership: memberOf=CN=HarborUsers,OU=CompanyGroups,DC=example,DC=netHarborUsers is the group in AD which has users allowed to access Harbor. This means you’ll need to add users to a group to be mapped here, so you don’t allow all users on AD.
Once all the values are provided, click “TEST LDAP SERVER” button to validate settings.
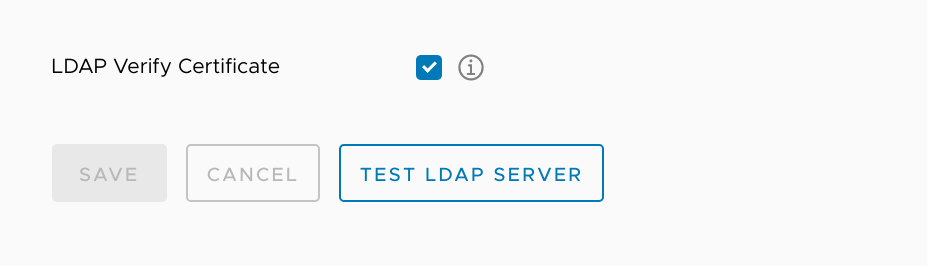
If the connection is successful, you’ll get this message.
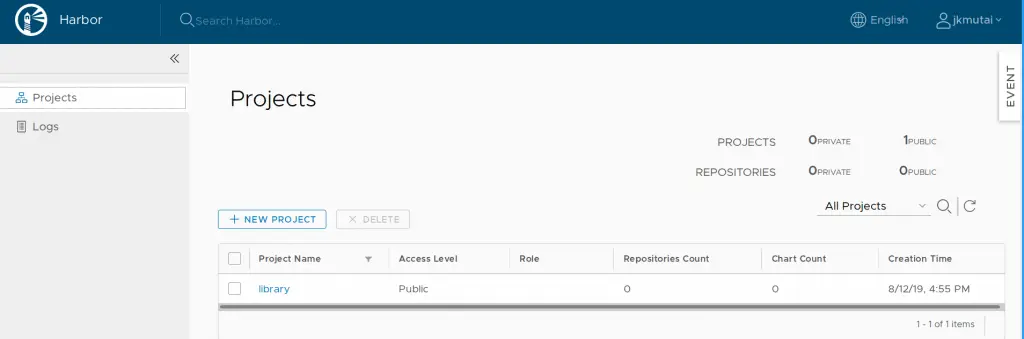
Test login on Harbor web portal to confirm users on your Active Directory group can access the service.
You need to authenticate to access Harbor registry on Docker machine.
$ docker login reg1.example.com Authenticating with existing credentials... Existing credentials are invalid, please enter valid username and password Username: computingforgeeks Password: <LDAPPassword> Login Succeeded!
Users can now login to Harbor image registry using Active Directory credentials.
More on image registries: