Configuring Cisco Switch Telnet Password,Using Telnet on Cisco Network, How to configure ssh and Telnet on Cisco IOS and Cisco Routers.
First we will begin by discussing what telnet is then proceed to get our hands dirty by doing the configuration.
What is Telnet?
Telnet is a part of the TCP/IP protocol suite. Telnet is a very powerful program that is used for interactive communication with another host using TELNET protocol. Telnet can check all the seven layers of OSI model.
Telnet is a virtual terminal protocol and its main work is to allow you to connect to remote devices and execute commands or run programs as if you were sitting on front of the device. If it is invoked with a host argument, it performs an open command implicitly. Telnet uses TCP port 23 to remotely connect to network devices.
The main disadvantage of Telnet is the true fact that it’s not secure. It sends packets in pure text. That means anybody who is eavesdropping on network traffic is able to see all our commands that we are sending to a remote device including user account information and login password. Many administrators nowadays are using Secure Shell (SSH) which encrypts data before sending them over the network medium. SSH on the other hand, uses TCP port 22.
See Routers and Catalyst Switch IOS CLI EDITING COMMANDS for must know editing commands that fasten your navigation on console window.
Since we are going to configure Telnet access on Cisco router, Let’s look at the commonly used Telnet commands.
- telnet: Command used to perform the connection to a remote device. It’s what makes your console a dumb terminal.
- show users: This is the command used to show devices that are connected to the router or switch using Telnet. It lists all active consoles and VTY ports in use on the router.
- show sessions: Used to show devices ( router/switches) that you are telnetted to. It shows connections made from your router to other devices on the network.
- disconnect: Used to end telnet session from a local device.. It closes a remote telnet session.
- exit: Used to close a telnet session
- clear line vty: It ends the session of a user connected to router’s VTY line.
Configure Telnet access on Cisco devices
To be able to use telnet on a router, you have to set VTY password or use the no login command since VTY ports on a router are configured as login.
On a Cisco router, it’s not a must you type telnet before specifying the IP address of a device to connect to, you can connect by just typing the IP address on the console and the router will assume you want to initiate a telnet session. For Example:
# telnet 192.168.100.2
# 192.168.100.2Will accomplish same task.
Pressing Ctrl+Shift+6 key combination followed by X gets you back to the router’s console without terminating telnet session. If you want to use hostname rather than IP address to connect to a remote device, a hostname need to be resolved to IP address. The easiest way to achieve this without the use of a fully qualified domain name (FQDN) is the use of host table.This won’t use Domain Name System (DNS) server.
The command to build a host table on a Cisco router is ip host hostname ip-address, e.g.
R1# config terminal
R1(config)# ip host R2 192.168.100.2To see the host table build, type show hosts command.
For our demo on configuring Telnet, we’ll use the topology shown below

We have two Routers R1 and R2.We will setup R1 as Telnet client and R2 as Telnet server. R2 will receive telnet sessions and authenticate users who telnet.
R1 configurations
Setting console synchronous and time-out to 00
$ enable
# configure terminal
# line console 0
# logging synchronous
# no exec-timeout
# do wr
# endConfiguring IP address information
# config t
# ip host R2 192.168.100.2
# interface fastEthernet 0/0
# ip address 192.168.100.1 255.255.255.0
# no shutdown
# do copy run start
# endR2 Configurations
$ enable
# configure terminal
# line console 0
# logging synchronous
# no exec-timeout
# do wr
# endConfigure R2 to Telnet to its VTY Lines:
# enable
# config t
# line vty 0 4
# login local
# exit
# username admin privilege 15 secret password!123
# endLogin local means any inbound connection trying to come in on the VTY lines, the router prompt for username and the password to validate users
We then added a user “admin” and gave him a password “password!123”. Using secret keyword encrypts the password in the configuration as opposed to password keyword which store it in a plain text.
Configuring IP address information, hostname.
# configure terminal
# ip host R1 192.168.100.1
# interface fastEthernet 0/0
# ip address 192.168.100.2 255.255.255.0
# no shutdown
# do copy run start
# end To test network connectivity, on R1 type:
# ping 192.168.100.2Test telnet connectivity
On R2 test connectivity to R1
# ping 192.168.100.1If the two devices can ping each other, then our network is working well.
To telnet to R2 from R1, let’s make a road trip to R1 then type:
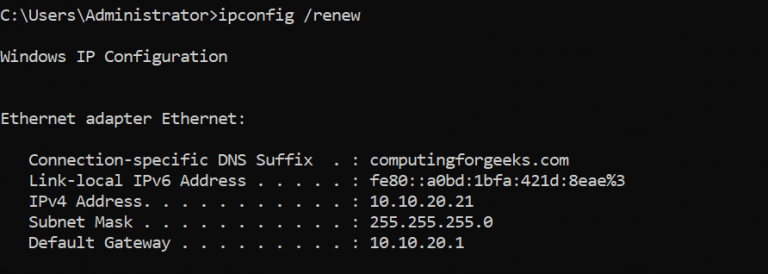
R1# telnet 192.168.100.2Then enter the login username “admin” and the password that you set, for my example, the password is “password!123”. To see the TCP port used by Telnet, on R2 type:
# show tcp briefIf you are using GNS3 for this test and have Wireshark installed, you can easily proof that telnet send all information in plain text. Just right click on the link between R1 and R2, select “start capture”.
Now, on R1 telnet to R2
# telnet 192.168.100.2Use the previously set account name and password, then open Wireshark and stop the capture. Right click on Telnet protocol with info “Telnet Data …” , click on “Follow TCP Stream“
From the results above, you can see that the username and password are revealed to us and the attacker would certainly see the same results. This is the reason why Telnet is not suitable for use in a production environment.
It is relatively simple to protect Telnet lines by permitting only SSH traffic in and out. Here are the commands to accomplish that.
# enable
# config t
# line console 0 15
# transport input ssh
# transport output sshThat’s all about setting up and configuring Telnet access on Cisco Routers. In our next tutorial we’ll talk about configuring SSH which is more secure.