The priority of KVM is security and by default it limits the management access to root users. If you want to run virt-manager without being asked for sudo password, then this article is for you. We will be using a group with correct permissions to manage KVM, this enables you to grant multiple users in the system permissions to administer KVM hypervisor.
In our previous guide we covered in detail the procedure of installing and configuring KVM hypervisor. With KVM installed and working, follow the steps below if you want to run Virt Manager without sudo permissions.
1) Create unix group for KVM
First check if group already exist, if not create it with commands below.
sudo getent group | grep libvirtSome distributions may be using libvirtd.
sudo getent group | grep libvirtdIf the group does’t exist add using groupadd command.
sudo groupadd --system libvirt2) Add users to the libvirt group
Add user to the group using the syntax.
sudo usermod -a -G libvirt <username>
newgrp libvirtExample of adding the current user account you are logged in as.
sudo usermod -a -G libvirt $(whoami)
newgrp libvirtConfirm that the user has been added to the group.
$ id cloudspinx
uid=1001(cloudspinx) gid=1001(cloudspinx) groups=1001(cloudspinx),986(libvirt)3) Edit libvirtd configuration file
Open Libvirtd configuration file /etc/libvirt/libvirtd.conf for editing.
# Using vim
sudo vim /etc/libvirt/libvirtd.conf
# Using nano
sudo nano /etc/libvirt/libvirtd.confFind the unix_sock_group line and uncomment to define domain socket group ownership for libvirtd, (around line 85)
unix_sock_group = "libvirt"Also assign UNIX socket permissions for the socket – we are setting R/W (around line 102)
unix_sock_rw_perms = "0770"When done with the changes restart libvirtd service.
sudo systemctl restart libvirtd.serviceConfirm service status:
$ systemctl status libvirtd.service
● libvirtd.service - Virtualization daemon
Loaded: loaded (/usr/lib/systemd/system/libvirtd.service; enabled; vendor preset: enabled)
Active: active (running) since Mon 2024-07-08 13:02:26 EAT; 19min ago
Docs: man:libvirtd(8)
https://libvirt.org
Main PID: 104329 (libvirtd)
Tasks: 27 (limit: 32768)
Memory: 94.5M
CGroup: /system.slice/libvirtd.service
├─ 1737 /usr/sbin/dnsmasq --conf-file=/var/lib/libvirt/dnsmasq/crc.conf --leasefile-ro --dhcp-script=/usr/libexec/libvirt_leaseshelper
├─ 1739 /usr/sbin/dnsmasq --conf-file=/var/lib/libvirt/dnsmasq/crc.conf --leasefile-ro --dhcp-script=/usr/libexec/libvirt_leaseshelper
├─ 1815 /usr/sbin/dnsmasq --conf-file=/var/lib/libvirt/dnsmasq/default.conf --leasefile-ro --dhcp-script=/usr/libexec/libvirt_leaseshelper
├─ 1816 /usr/sbin/dnsmasq --conf-file=/var/lib/libvirt/dnsmasq/default.conf --leasefile-ro --dhcp-script=/usr/libexec/libvirt_leaseshelper
└─104329 /usr/sbin/libvirtd --timeout 120
Jul 08 13:02:26 kvm01.home.cloudlabske.io systemd[1]: Starting Virtualization daemon...
Jul 08 13:02:26 kvm01.home.cloudlabske.io systemd[1]: Started Virtualization daemon.
Jul 08 13:02:26 kvm01.home.cloudlabske.io dnsmasq[1815]: read /etc/hosts - 2 addresses
Jul 08 13:02:26 kvm01.home.cloudlabske.io dnsmasq[1737]: read /etc/hosts - 2 addresses
Jul 08 13:02:26 kvm01.home.cloudlabske.io dnsmasq[1737]: read /var/lib/libvirt/dnsmasq/crc.addnhosts - 0 addresses
Jul 08 13:02:26 kvm01.home.cloudlabske.io dnsmasq[1815]: read /var/lib/libvirt/dnsmasq/default.addnhosts - 0 addresses
Jul 08 13:02:26 kvm01.home.cloudlabske.io dnsmasq-dhcp[1815]: read /var/lib/libvirt/dnsmasq/default.hostsfile
Jul 08 13:02:26 kvm01.home.cloudlabske.io dnsmasq-dhcp[1737]: read /var/lib/libvirt/dnsmasq/crc.hostsfileLaunch virt-manager and test
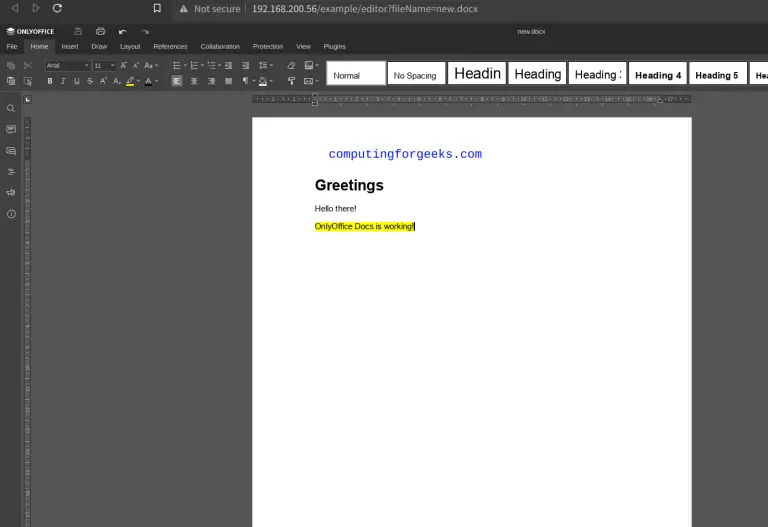
Open your terminal and launch Virt Manager. You can also use GUI launcher.
virt-managerYou should be able to connect without any permissions being asked.

That’s all on how to allow non-root users to manage VMs on KVM using virshor virt-manager without sudo permissions.
Check more articles available on KVM.
- Using Vagrant with Libvirt on Linux.
- How to Provision VMs on KVM with Terraform
- How to Create CentOS / Fedora / RHEL VM Templates on KVM
- RHEL and CentOS Kickstart on KVM Automated Installation With virt-install
Further reading:



Hi, i tried to store all my virtual machines on nfs or samba share but i have a lot of problems with permission. I can create volumes but i can’t create virtual machines. The nfs or samba shares are on synology machine.
Unable to complete install: ‘internal error: child reported: unable to set user and group to ‘107:107’ on ‘/mnt/smb/centos7.0.qcow2′: Permission denied’
Hi,
Please Change group ownership for the directory to kvm and retry. It should work fine.
Thanks for the reply, I changed permissions a thousand time, even changed my nfs server operating system once (synology and freenas), nothing worked. Today I found a solution, I do not know if it is safe to do this but it worked: setenforce 0.
Please try this:
Find kvm group ID:
# getent group kvm
kvm:x:36:qemu,sanlock
Then configure your nfs export with below options:
..(rw,anonuid=36,anongid=36,all_squash)
Replace 36 with your KVM group id.
Re-export:
# exportfs -rvv
Let me know if this helps.