This guide will help you to Install OSSEC HIDS on Ubuntu / Debian. OSSEC is an open source host-based intrusion detection system (HIDS) that runs on Linux, OpenBSD, Solaris, FreeBSD, Windows, and other systems. OSSEC works in a server/client model. The OSSEC client performs log analysis, policy monitoring, file integrity checking, real-time alerting, rootkit detection and active response.
OSSEC has the aspects of HIDS (host-based intrusion detection), log monitoring and SIM/SIEM as a simple solution with Web UI management.
Step 1: Install OSSEC Dependencies
OSSEC requires PHP, gcc, libc and Apache Web Server. Install them by running the commands below:
sudo apt update
sudo apt install -y wget curl unzip make gcc build-essential
sudo apt install -y php php-cli php-common libapache2-mod-php apache2-utils sendmail inotify-toolsStep 2: Install OSSEC HIDS on Ubuntu / Debian
Once the dependencies have been installed, the next installation is for OSSEC HIDS. The source code for OSSEC is available on Github.
Check for the latest release before downloading.
VER=$(curl -s https://api.github.com/repos/ossec/ossec-hids/releases/latest|grep tag_name|cut -d '"' -f 4)
wget https://github.com/ossec/ossec-hids/archive/${VER}.tar.gzOnce downloaded, extract the file with the following command:
tar xvf $VER.tar.gzThis extraction will create a folder, change to this folder and run the install script:
cd ossec-hids-${VER}
sudo ./install.sh1. Set language
(en/br/cn/de/el/es/fr/hu/it/jp/nl/pl/ru/sr/tr) [en]: en2. Press <ENTER> to continue
OSSEC HIDS v3.1.0 Installation Script - http://www.ossec.net
You are about to start the installation process of the OSSEC HIDS.
You must have a C compiler pre-installed in your system.
- System: Linux jammy 5.15.0-72-generic
- User: root
- Host: jammy
-- Press ENTER to continue or Ctrl-C to abort. --3. Choose local installation type
What kind of installation do you want (server, agent, local, hybrid or help)? localWith the local installation, you will be able to do everything the server does, except receiving remote messages from the agents or external syslog devices.
4. Choose where to install the OSSEC HIDS [/var/ossec], press enter to use /var/ossec
Installation will be made at /var/ossec .5. Configuring the OSSEC HIDS
3.1- Do you want e-mail notification? (y/n) [y]: y
- What's your e-mail address? [email protected]
- What's your SMTP server ip/host? localhost
3.2- Do you want to run the integrity check daemon? (y/n) [y]: y
- Running syscheck (integrity check daemon).
3.3- Do you want to run the rootkit detection engine? (y/n) [y]: y
- Running rootcheck (rootkit detection).
3.4- Active response allows you to execute a specific
command based on the events received. For example,
you can block an IP address or disable access for
a specific user.
More information at:
http://www.ossec.net/en/manual.html#active-response
- Do you want to enable active response? (y/n) [y]: y
- Active response enabled.
- By default, we can enable the host-deny and the
firewall-drop responses. The first one will add
a host to the /etc/hosts.deny and the second one
will block the host on iptables (if linux) or on
ipfilter (if Solaris, FreeBSD or NetBSD).
- They can be used to stop SSHD brute force scans,
portscans and some other forms of attacks. You can
also add them to block on snort events, for example.
- Do you want to enable the firewall-drop response? (y/n) [y]: y
- firewall-drop enabled (local) for levels >= 6
- Default white list for the active response:
- 192.168.121.1
- Do you want to add more IPs to the white list? (y/n)? [n]:
3.6- Setting the configuration to analyze the following logs:
-- /var/log/messages
-- /var/log/auth.log
-- /var/log/syslog
-- /var/log/mail.info
-- /var/log/dpkg.log
-- /var/log/apache2/error.log (apache log)
-- /var/log/apache2/access.log (apache log)
- If you want to monitor any other file, just change
the ossec.conf and add a new localfile entry.
Any questions about the configuration can be answered
by visiting us online at http://www.ossec.net .
--- Press ENTER to continue ---Press Enter to start the installation
The init script for managing OSSEC HIDS is /var/ossec/bin/ossec-control
To start the service, use:
$ sudo /var/ossec/bin/ossec-control start
Starting OSSEC HIDS v3.7.0 (by Trend Micro Inc.)...
Started ossec-maild...
Started ossec-execd...
Started ossec-analysisd...
Started ossec-logcollector...
Started ossec-syscheckd...
Started ossec-monitord...
Completed.And stop it by running
sudo /var/ossec/bin/ossec-control stopYou can further configure OSSEC HIDS by editing the configuration file:
sudo vim /var/ossec/etc/ossec.conf
The rules are located under the directory/var/ossec/rules/. The rules for local system files are set on the file /var/ossec/rules/local_rules.xml
Check OSSEC Documentation for configuration options.
Don’t forget to restart OSSEC HIDS whenever you make a change
sudo /var/ossec/bin/ossec-control restartStep 3: Install OSSEC Web UI
OSSEC HIDS has a simple web interface, but it needs to be installed.
git clone https://github.com/ossec/ossec-wui.git
sudo mv ossec-wui /srv
cd /srv/ossec-wui
sudo ./setup.shSet Dashboard admin username/password and web server username
trap: SIGHUP: bad trap
Setting up ossec ui...
Username: admin
New password: <ENTER PASSWORD>
Re-type new password:<CONFIRM PASSWORD>
Adding password for user admin
Enter your web server user name (e.g. apache, www, nobody, www-data, ...)
www-data
You must restart your web server after this setup is done.
Setup completed successfully.Create an Apache VirtualHost configuration file
sudo vim /etc/apache2/sites-enabled/ossec-wui.confPut the contents below into the file
<VirtualHost *:80>
DocumentRoot /srv/ossec-wui/
ServerName ossec.example.com
ServerAlias www.ossec.example.com
ServerAdmin [email protected]
<Directory /srv/ossec-wui/>
Options +FollowSymlinks
AllowOverride All
Require all granted
</Directory>
ErrorLog /var/log/apache2/moodle-error.log
CustomLog /var/log/apache2/moodle-access.log combined
</VirtualHost>Replace example.com with your domain name, save the file and exit.
Enable the Apache rewrite module
sudo a2enmod rewrite
sudo systemctl restart apache2$ systemctl status apache2.service
● apache2.service - The Apache HTTP Server
Loaded: loaded (/lib/systemd/system/apache2.service; enabled; vendor preset: enabled)
Active: active (running) since Thu 2023-06-01 19:14:31 UTC; 11s ago
Docs: https://httpd.apache.org/docs/2.4/
Main PID: 7580 (apache2)
Tasks: 55 (limit: 4537)
Memory: 5.1M
CPU: 54ms
CGroup: /system.slice/apache2.service
├─7580 /usr/sbin/apache2 -k start
├─7582 /usr/sbin/apache2 -k start
└─7583 /usr/sbin/apache2 -k startOpen http://ossec.example.com in your web browser and authenticate to the dashboard.
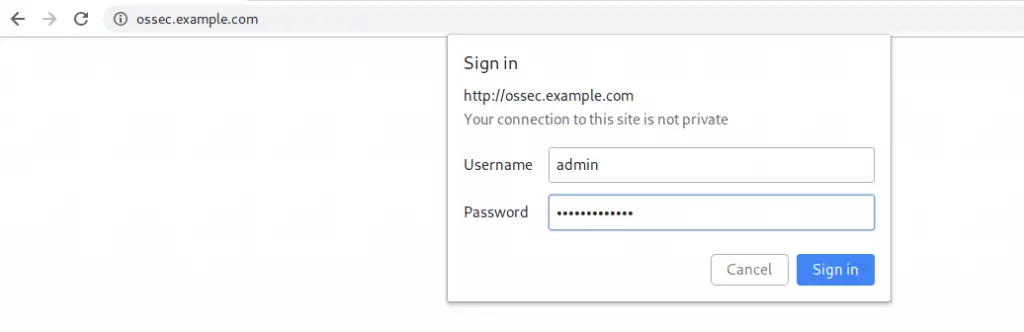
On Login. you should get a page like below:
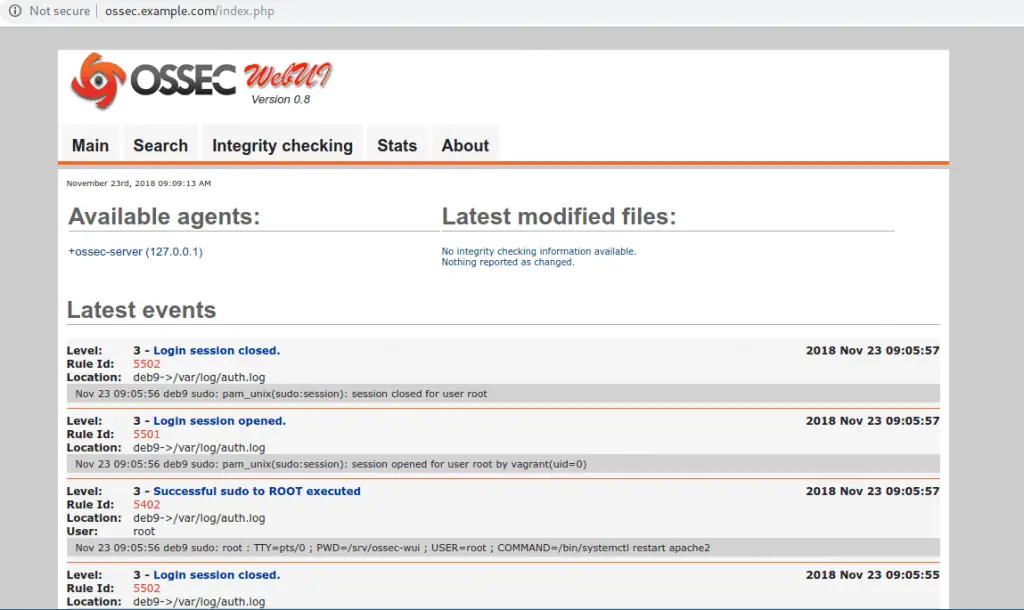
This marks the end of install OSSEC HIDS on Ubuntu / Debian article.
Recommended Security Books to read:
- Best Penetration Testing Books
- Best Cybersecurity Books To Read
- Best CompTIA Security+ (SY0-601) Certification Books
- Top Certified Information Security Manager (CISM) study books
References:
